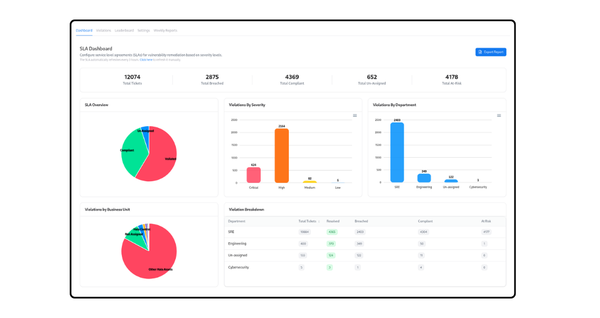
product
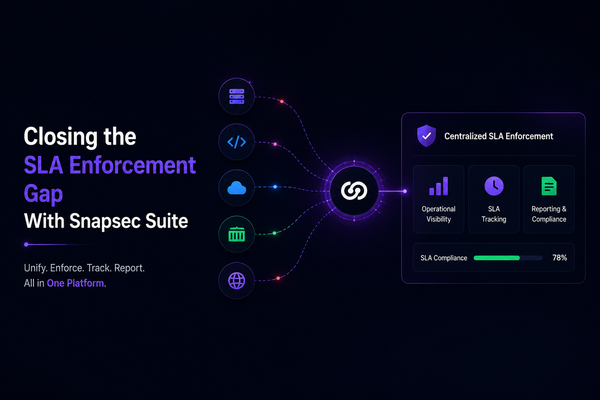
Closing the SLA Enforcement Gap With Snapsec Suite
Most companies today use multiple security tools to detect vulnerabilities. Findings come from infrastructure scanners, SAST platforms, cloud security tools, container security platforms, and external attack surface monitoring solutions. The real challenge starts after detection. Vulnerabilities become scattered across different dashboards, ticketing systems, spreadsheets, and workflows. Every tool follows its