Shadow IT and SAMA Compliance: The Gap No One Owns
SAMA’s Cyber Security Framework enforces disciplined control across asset management, access control, vulnerability management, and continuous monitoring. It assumes that organizations maintain complete visibility of their assets, assign clear ownership, and enforce controls consistently across the environment. In structured environments, this model works.
In modern environments, it breaks.
Compliance does not fail because controls are weak.
It fails because visibility and ownership are incomplete.
Shadow IT is no longer an edge case—it is a byproduct of how systems are built today. Development teams deploy services outside central onboarding workflows, spin up cloud resources in separate accounts, expose APIs for integrations, and create subdomains for temporary use. These assets are not intentionally hidden—they are simply never brought into governance.
The Assumption That Fails: Ownership and Visibility
SAMA controls rely on two implicit conditions: that assets are known, and that each asset has an accountable owner. These assumptions underpin vulnerability management, access enforcement, logging, and monitoring.
When either condition breaks, controls do not degrade—they silently stop applying.
Shadow IT exists precisely in this gap. Assets without ownership are not assigned to teams. Assets without visibility are not included in scans. The framework continues to operate correctly, but only over assets that meet its assumptions.
This creates a structural condition where compliance is enforced on a subset of the environment, while the rest remains ungoverned.
Where Shadow IT Actually Lives
In practice, shadow IT is not buried deep inside internal systems—it is often externally reachable and operationally active. It appears in predictable but weakly governed layers such as subdomains created for campaigns or testing, APIs exposed through unmanaged gateways, cloud resources deployed in secondary accounts, and integrations that introduce externally accessible endpoints.
This is where shadow IT becomes visible in practice:
These assets frequently lack basic controls such as authentication hardening, logging, patching, and vulnerability scanning. More critically, they lack visibility—they are not part of the systems that would detect or remediate these issues.
Why This Gap Is Systemic
This is not a tooling failure, it is a control design limitation.
SAMA defines what must be done to assets, but not how to ensure that all assets are continuously identified. Asset inventory is treated as a prerequisite rather than a continuously validated control. In static environments, this distinction is manageable. In dynamic environments, it becomes the primary failure point.
Organizations typically implement onboarding workflows, periodic discovery, and ownership tagging during provisioning. However, these mechanisms assume that assets are created through governed paths. Shadow IT exists outside those paths. Once an asset bypasses onboarding, there is no native mechanism to bring it back into scope automatically.
The Risk Model Breaks Down
Risk management under SAMA is driven by identified assets, classified data, and measured vulnerabilities. Shadow IT disrupts all three simultaneously.
Assets are not identified, so they do not exist in risk registers. Data exposure is unknown, so classification does not apply. Vulnerabilities are never scanned, so risk scoring remains incomplete.
This leads to a critical condition: risk is not just unmitigated—it is unmeasured.
From a reporting perspective, dashboards remain clean, SLAs are met, and controls appear effective. From an attacker’s perspective, shadow IT represents low-friction entry points outside monitoring and response workflows.
The Accountability Vacuum
Shadow IT introduces not just a technical gap, but an organizational one.
If an asset is not in inventory, it is not assigned to a team. If it has no owner, it has no SLA. If it has no SLA, it has no urgency.
This creates an accountability vacuum where no team is responsible for remediation, no alerts are routed for response, and no audit trail exists for changes or access.
The issue is not that controls are weak—it is that no one is accountable for applying them.
Why This Should Concern Regulators
SAMA’s framework is designed to ensure systemic resilience across financial institutions. However, the current model validates control implementation within a defined scope—it does not validate the completeness of that scope in real time.
This creates a regulatory blind spot. Organizations can demonstrate control maturity, pass audits, and show reduced risk metrics, while still operating with unmanaged and externally exposed assets.
The implication is not non-compliance—it is incomplete compliance with unbounded exposure.
Bridging the Shadow IT Gap with Continuous Discovery
The gap created by shadow IT cannot be addressed through traditional inventory or governance workflows. It requires a control layer that operates independently of internal registration and continuously identifies assets as they appear.
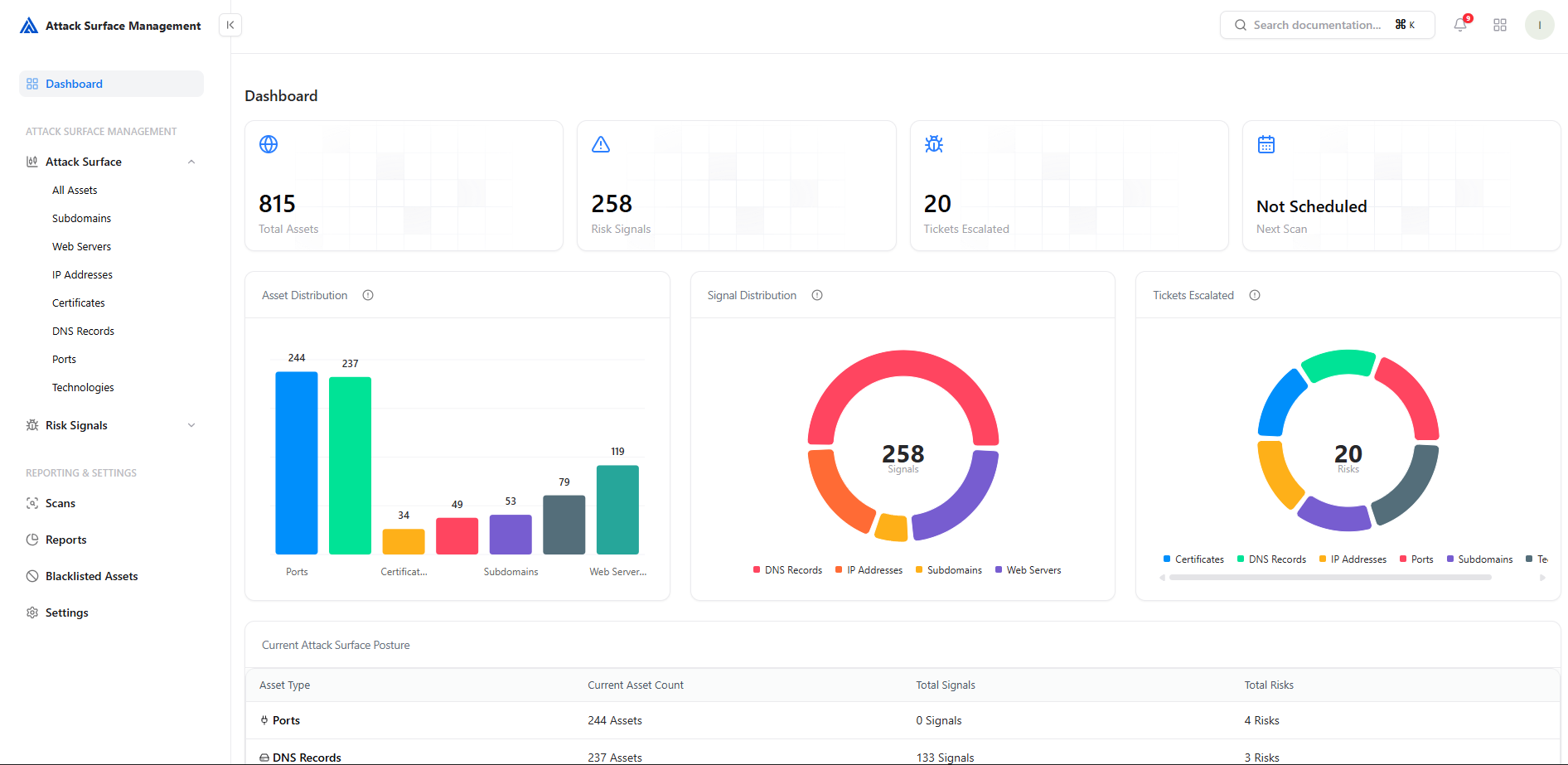
This is where Snapsec’s Attack Surface Management (ASM) becomes critical.
Snapsec ASM continuously discovers externally reachable assets across domains, subdomains, IP ranges, and APIs, without relying on predefined asset lists. It identifies assets that exist outside traditional inventory systems and brings them into visibility in real time. This ensures that shadow IT is not treated as an exception, but as part of the monitored environment.
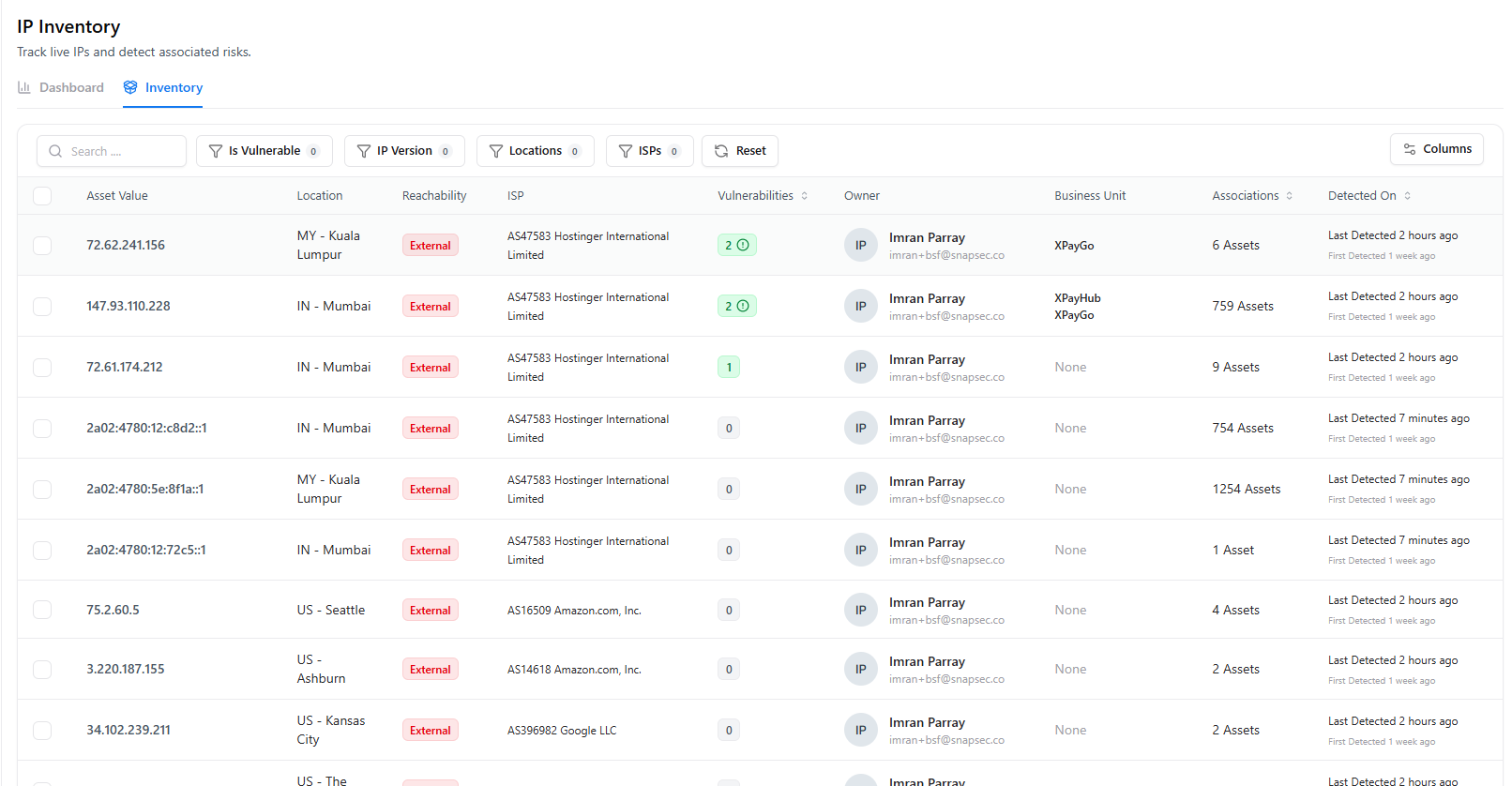
Once discovered, assets are enriched with context such as exposure, ownership signals, and risk indicators. This allows organizations to immediately bring unmanaged assets under governance—assign ownership, include them in vulnerability scanning, and enforce controls without delay.
By shifting asset discovery from a periodic activity to a continuous control, Snapsec closes the gap between what is deployed and what is governed.
Closing Thought
Shadow IT is not an exception to SAMA compliance, it is a condition that exists outside its assumptions.
Until asset discovery is continuous and ownership is enforced at the point of discovery, organizations are not managing their full environment. They are managing the portion they can see.
And in that unseen portion, no control applies,because no one owns it.