Why SAMA Compliance Fails Without Continuous Attack Surface Discovery

SAMA’s Cyber Security Framework is a risk-based control model that enforces asset management, vulnerability management, and continuous monitoring across regulated institutions. It requires organizations to identify all information assets, assess their risk, and apply security controls through defined processes and remediation timelines. In theory, this creates a complete lifecycle, from asset identification to vulnerability remediation, supported by audits and maturity-based evaluations.
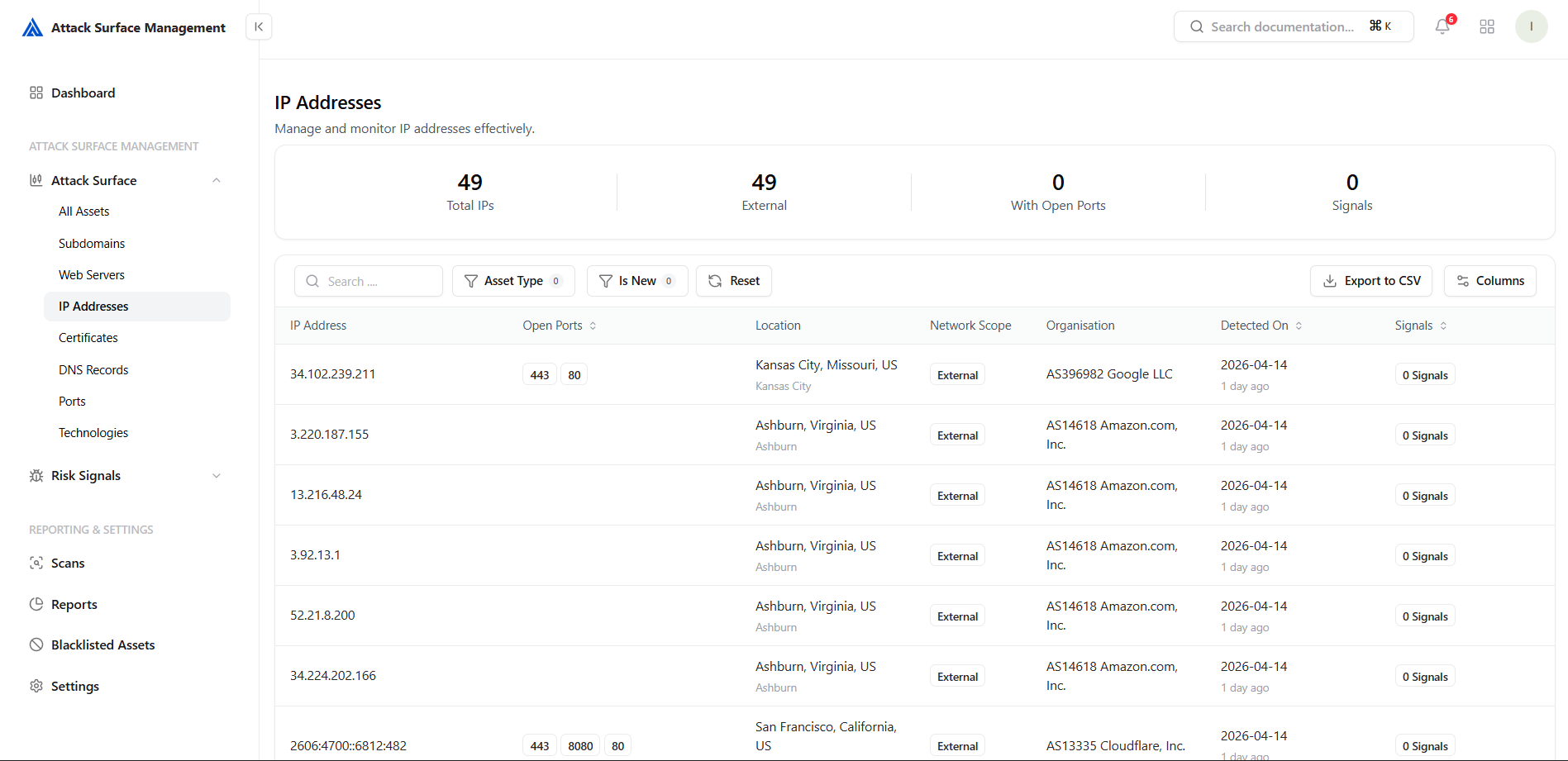
However, this entire model depends on a critical prerequisite: a complete and accurate asset inventory. SAMA mandates that vulnerability management applies to all assets, but it does not define how those assets are continuously discovered. In practice, organizations rely on CMDBs, internal registers, and periodic scans, all of which introduce delay. As a result, compliance operates on what is recorded, not necessarily on what exists.
Compliance does not fail because controls are weak. It fails because visibility is incomplete.
This gap becomes more visible in modern environments where assets are created dynamically across cloud platforms, APIs, and subdomains. Controls like scanning and patching assume assets are already known, but anything outside that visibility is automatically excluded. This creates a situation where organizations remain compliant, processes are followed, and SLAs are met, yet parts of the attack surface remain untracked and exposed.
The Core Dependency: Asset Visibility
Every major control in SAMA, whether vulnerability management, patching, or risk assessment, assumes that the asset scope is complete. The framework requires organizations to scan assets, classify vulnerabilities, and remediate them within defined timelines. In reality, these controls only operate on assets that are already known and registered.
This creates a direct dependency between asset visibility and control effectiveness. If an asset is missing from inventory, it is excluded from scans, risk calculations, and compliance reporting. The control itself does not fail, it simply never applies. Over time, this leads to a situation where vulnerability management appears effective but is limited to a subset of the environment.
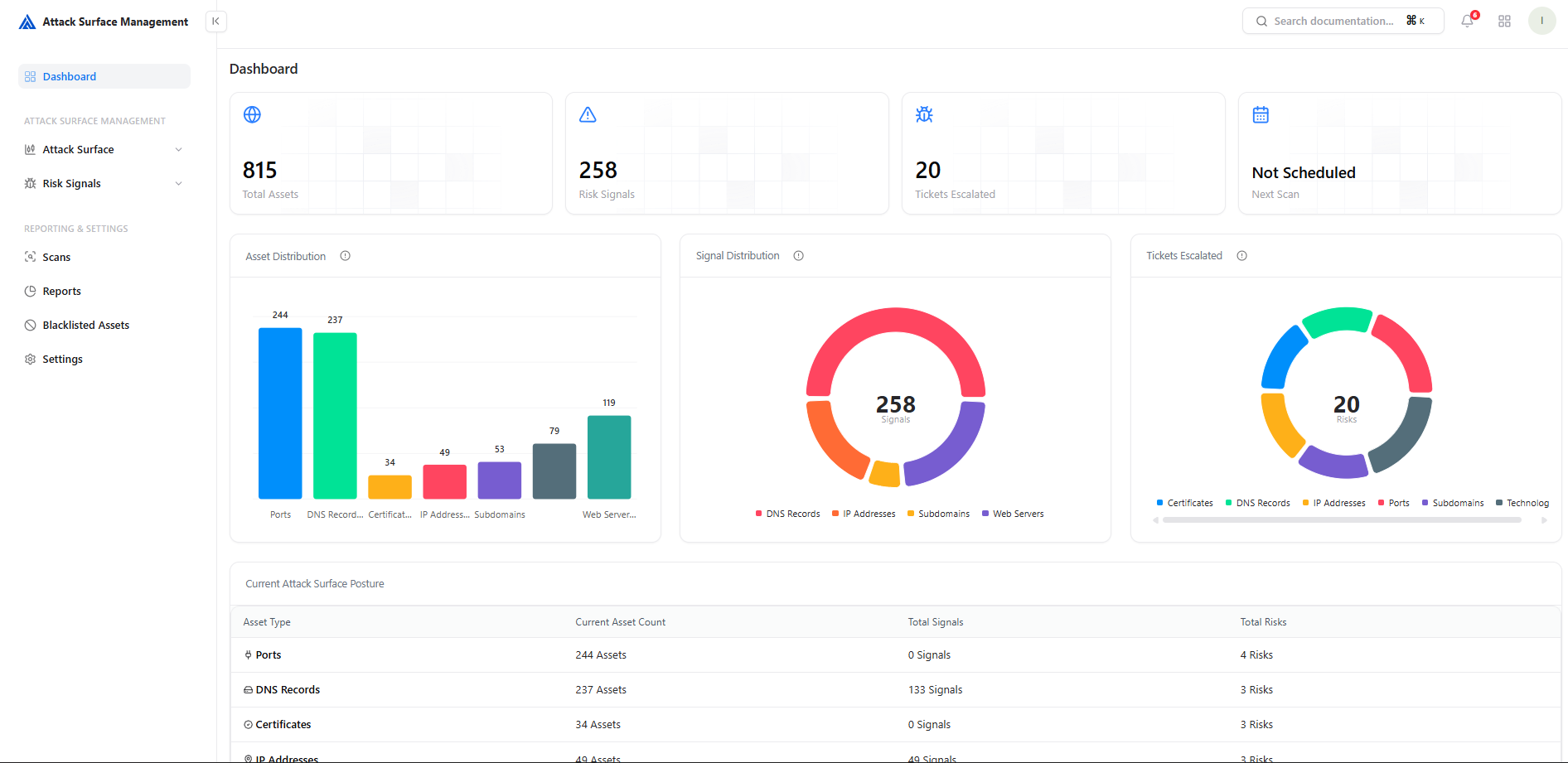
This is where continuous, real-time asset visibility becomes essential to ensure that all assets, known or unknown, are brought under security controls, along with their exposure and risk context.
The Operational Blind Spot
SAMA compliance ensures that processes are defined and executed, but it does not guarantee complete coverage. Security teams operate within the boundaries of known assets, and anything outside that boundary remains unaccounted for. This creates an operational blind spot where controls function correctly, but within a limited scope.
In practice, teams continue scanning, patching, and closing vulnerabilities across visible assets, while unknown or unmanaged assets remain outside every control layer. These are often externally reachable systems, APIs, subdomains, or cloud resources that were never included in inventory. The issue is not that controls are failing, but that they operate on an incomplete view of the environment.
Why Continuous Discovery Is Not Optional
SAMA’s controls assume asset visibility is already complete, but in modern environments this is not a static condition, it is continuous. Assets are created, modified, and exposed in real time, which means visibility must operate at the same speed. Periodic discovery and manual updates cannot keep up with this rate of change.
Without continuous attack surface discovery, this gap becomes persistent. New assets remain outside visibility, exposure changes go unnoticed, and security controls continue to operate on incomplete data. Compliance may reflect a controlled environment, but the actual attack surface evolves independently.
The Missing Control Layer
SAMA defines controls for managing assets, vulnerabilities, and risk, but it does not explicitly define a control for continuous external asset discovery. It assumes that asset identification is already complete and maintained through governance processes. In modern environments, this assumption creates a gap where discovery is treated as a supporting activity rather than a primary control.
In practice, continuous attack surface discovery acts as a missing layer that sits before everything else. It ensures that assets are identified as they appear, brought into inventory immediately, and subjected to security controls without delay. Without this layer, all downstream controls operate on partial visibility.
Without this layer, organizations are not managing risk, they are managing a subset of it.
Why This Matters in Regulated Environments
In regulated environments, compliance is often treated as a proxy for security. Regulatory frameworks like SAMA are designed to enforce discipline, standardization, and accountability across organizations. However, when asset visibility is incomplete, compliance can create a false sense of assurance—where controls appear effective, but only within a limited and predefined scope.
This becomes a critical risk at the leadership level. Decisions around risk acceptance, remediation prioritization, and security investment are made based on reported data. If that data does not reflect the full attack surface, organizations are not just underestimating risk—they are operating with false confidence. In such environments, unknown exposure is more dangerous than known vulnerability, because it remains outside both control and awareness.
Closing the Visibility Gap
Closing this gap requires a shift from inventory-based security to visibility-driven security. Instead of relying on predefined asset lists, organizations need continuous discovery mechanisms that identify assets as they appear, track exposure in real time, and ensure they are immediately brought under control.
Continuous attack surface discovery aligns security operations with actual infrastructure. It ensures that vulnerability management, risk assessment, and remediation processes operate on complete and current data. Without it, compliance will continue to validate processes within a limited scope, while real exposure exists outside it.
The gap is not in compliance, it is in visibility.
Explore Snapsec Suite Now
Explore Snapsec Suite to see how you can unify asset visibility, prioritize real risk with True Risk, and manage vulnerabilities from a single platform. Get a clear, actionable view of your security posture and start fixing what truly matters, faster and more efficiently.