Fixing the CVSS Problem: How Normalization Improves Vulnerability Prioritization

The Common Vulnerability Scoring System (CVSS) is widely used to assign severity to vulnerabilities, but it is not designed to function as a prioritization mechanism. Its primary purpose is to provide a standardized way to describe vulnerabilities based on exploitability and impact using a generic scoring model. This model assumes a uniform environment and does not account for how vulnerabilities exist within real-world systems.
In practice, vulnerability risk is highly dependent on contextual factors such as asset exposure, network position, data sensitivity, authentication controls, and business criticality. CVSS does not incorporate any of these variables. As a result, the same vulnerability will receive the same score regardless of whether it is deployed on an internal, access-restricted system or an internet-facing production service handling sensitive data.
This creates a fundamental limitation. CVSS reflects theoretical severity, not operational risk. Two vulnerabilities with identical scores can have vastly different risk profiles depending on where they exist and how they are exposed. Without incorporating environmental context, CVSS cannot accurately represent which vulnerabilities should be prioritized for remediation.
Misprioritization and Operational Impact
Using CVSS directly for prioritization leads to consistent misclassification of risk. Vulnerabilities with high scores but limited exploitability are often prioritized, while lower-scored vulnerabilities on exposed or critical systems may be overlooked despite presenting real attack paths.
This results in inefficient vulnerability management workflows. Remediation queues become filled with findings that do not significantly reduce risk, while impactful vulnerabilities remain unresolved. Teams spend more time on triage and re-prioritization than on actual remediation, reducing overall effectiveness.
Over time, this degrades the quality of prioritization. Backlogs increase, SLA tracking becomes unreliable, and effort is misaligned with actual risk reduction. The core issue is not vulnerability detection, but the absence of context in how severity is interpreted and acted upon.
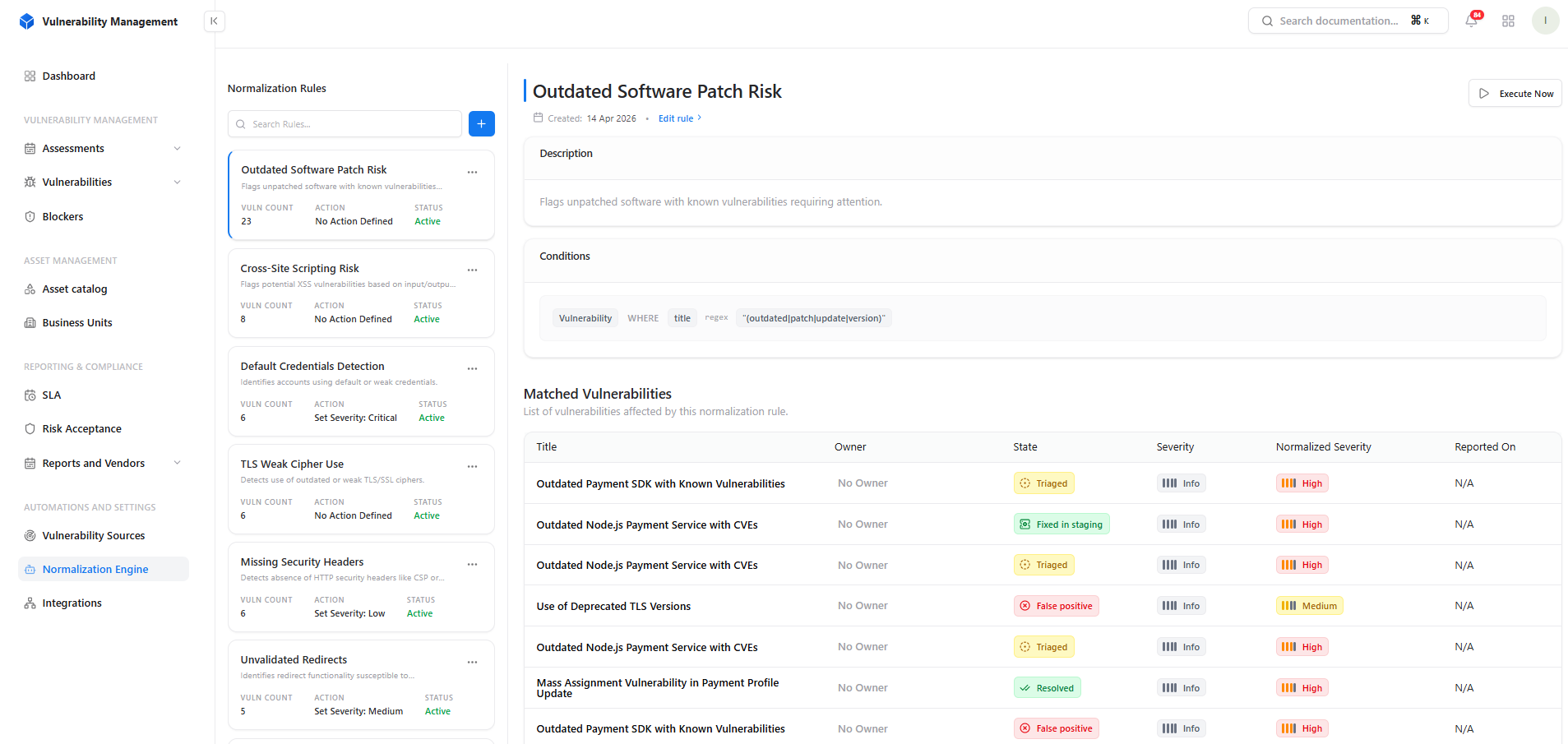
Snapsec Normalization Engine as a Severity Control
Normalization introduces a control layer on top of CVSS that allows severity to be adjusted based on environmental context. Instead of treating CVSS as final, severity becomes a dynamic attribute that can be re-evaluated using rules aligned with actual risk.
At Snapsec, this is implemented through a Normalization Engine that enables organizations to define how vulnerabilities should be prioritized within their own environment. This shifts prioritization from a static scoring model to a context-aware system. Vulnerabilities are no longer treated equally across systems; their severity can be downgraded if they exist in controlled conditions or escalated if they appear on exposed, high-impact assets.
This approach allows severity to reflect factors such as:
- Asset exposure and network position
- Business criticality of the system
- Sensitivity of the data involved
- Organizational risk tolerance
By decoupling prioritization from raw CVSS scores, Snapsec’s normalization layer ensures that decisions are driven by real exposure and business impact rather than theoretical severity.
Implementation: Rule-Based Severity Adjustment
Normalization is implemented through a rule-based system that evaluates vulnerabilities against contextual conditions and assigns an updated severity accordingly. Instead of relying solely on scanner output, the system applies organization-specific logic to determine how each vulnerability should be prioritized.
Each rule is structured into two distinct components: Conditions and Actions. Conditions define the criteria used to identify relevant vulnerabilities, while actions define how the severity should be modified once a match is found.
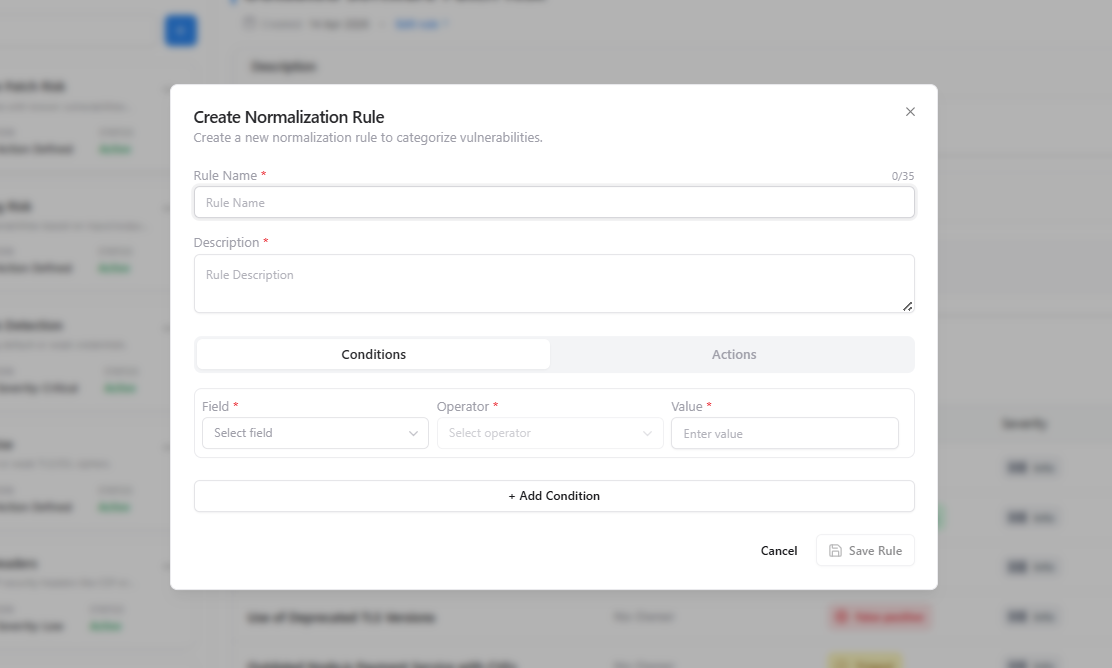
Conditions are defined using a structured format consisting of:
- Field (e.g., vulnerability title, tags, asset attributes)
- Operator (e.g., equals, contains, regex)
- Value (the condition to match against)
This enables precise targeting of vulnerability groups based on how they appear within the system.
Once conditions are defined, Actions determine how matched vulnerabilities are handled. The system supports two types of actions:
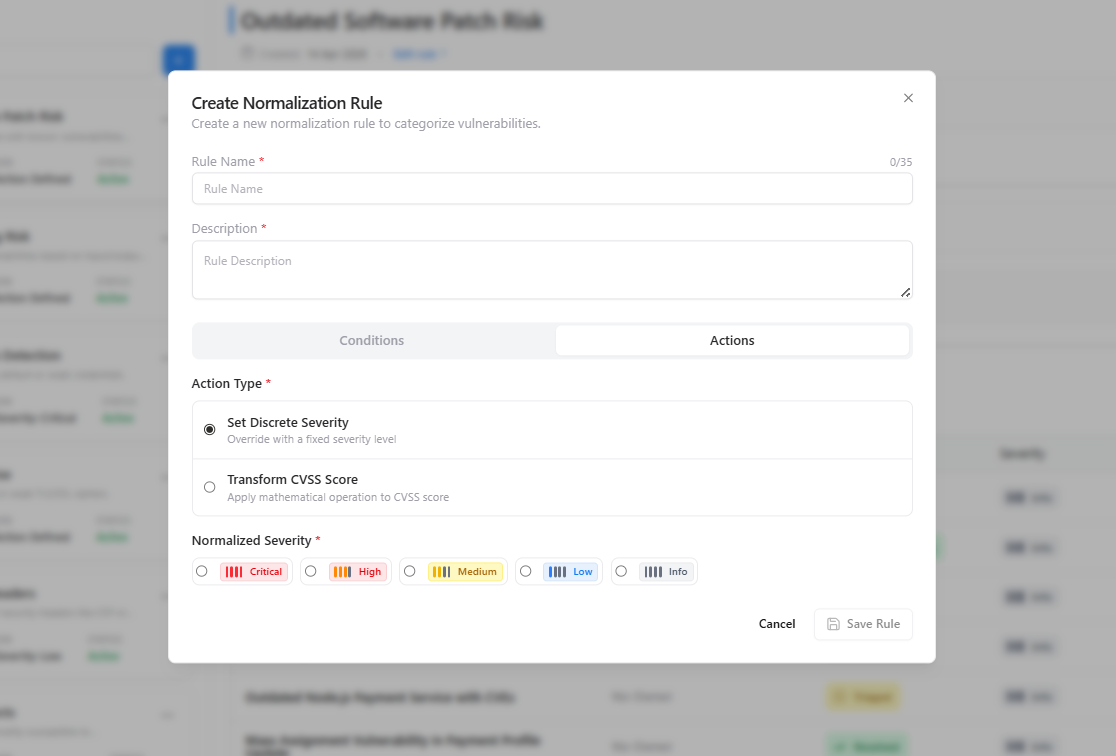
- Set Discrete Severity
Override the vulnerability severity with a fixed level such as Critical, High, Medium, Low, or Info. - Transform CVSS Score
Apply a mathematical transformation to the existing CVSS score to adjust severity dynamically.
When using discrete severity, the normalized severity is explicitly selected based on organizational prioritization policies, ensuring consistent classification across similar vulnerabilities.
Once configured, rules are automatically applied across all vulnerabilities, continuously evaluating findings and updating severity wherever conditions are satisfied.
By separating detection from severity assignment, this model makes prioritization deterministic, reducing triage effort while ensuring prioritization reflects actual risk.
Correcting Misclassification with Normalization
Normalization addresses the core limitation of CVSS by correcting how vulnerabilities are classified in real environments. Instead of treating severity as a fixed attribute, it enables re-evaluation based on contextual signals such as exposure, asset criticality, and data sensitivity. This removes the assumption that a vulnerability carries the same risk across all systems.
In practice, vulnerabilities with high CVSS scores but low practical exploitability—such as those on internal or restricted systems, can be downgraded to reflect their true impact. Conversely, vulnerabilities with moderate scores that exist on internet-facing or business-critical services can be escalated, ensuring they are prioritized appropriately despite lower baseline scoring.
This approach eliminates the distortion caused by static severity models and replaces it with context-driven classification. As a result, prioritization becomes aligned with actual risk, reducing false urgency while ensuring that genuinely impactful vulnerabilities are surfaced and addressed first.
Impact on Vulnerability Management
Applying normalization fundamentally changes how vulnerability management operates by aligning prioritization with actual risk rather than static scoring. Instead of large queues dominated by high CVSS findings, teams work on a refined set of vulnerabilities that are relevant to their environment and exposure.
At Snapsec, this translates into a significant reduction in prioritization noise. Vulnerabilities that do not meaningfully impact the organization are automatically deprioritized, while high-risk exposures are surfaced early. This reduces the time spent on triage and shifts focus toward remediation that directly lowers risk.
Over time, this leads to more predictable remediation workflows, improved SLA accuracy, and better coordination between security and engineering teams. The outcome is not just operational efficiency, but a measurable improvement in how quickly and effectively real vulnerabilities are identified and resolved.
Conclusion
CVSS remains a useful baseline for describing vulnerabilities, but it is not sufficient for prioritization. Its lack of environmental context leads to consistent misclassification, where effort is driven by scores rather than actual risk.
Normalization introduces the missing layer by allowing severity to be adjusted based on how vulnerabilities exist within a specific environment. By incorporating factors such as exposure, asset criticality, and business impact, it transforms prioritization into a context-aware process.
With Snapsec’s normalization engine, organizations move beyond static scoring and toward risk-driven decision-making. The result is clear: reduced noise, better prioritization, and faster remediation of vulnerabilities that actually matter.