One-Time Penetration Testing: Why It’s Bad for Your Company

For years, penetration testing has been treated as a milestone rather than a capability. Organizations schedule a test, receive a report, remediate a subset of findings, and move on, often for another six or twelve months. On paper, this satisfies compliance requirements and gives leadership a sense of assurance.
In practice, it creates a dangerous illusion of security.
Modern infrastructure does not stand still. Cloud environments change daily. CI/CD pipelines deploy continuously. New endpoints, APIs, configurations, and third-party integrations appear and disappear without ceremony. Against this backdrop, a point-in-time penetration test is not just insufficient—it is structurally misaligned with how systems actually operate.
The problem is not penetration testing itself. The problem is treating it as an event instead of a process.
Why One-Time Penetration Testing Fails in Modern Environments
Traditional penetration testing assumes a relatively stable environment. The test captures a snapshot, evaluates attack paths available at that moment, and reports findings based on that frozen state. Everything that happens after the test ends is implicitly out of scope.
This assumption no longer holds.
Between two penetration tests, organizations typically introduce:
- New application features
- Infrastructure changes through IaC
- Cloud service configuration drift
- New vendor integrations
- Temporary exposures that become permanent
- Credential and permission changes
None of these changes are reflected in the penetration test report that leadership continues to rely on.
As a result, security teams end up answering the wrong question. Instead of asking “Are we secure today?”, they are forced to say “We were secure when we last tested.” That gap is where real-world breaches occur.
The Core Issue: Penetration Testing Lacks Change Awareness
The fundamental weakness of one-time penetration testing is not coverage, it is blindness to change.
Pen tests do not understand:
- What changed after the test
- Whether a previously fixed issue reappeared
- Whether a new deployment reintroduced an old attack path
- Whether risk increased or decreased since the last assessment
Every infrastructure change is a potential security regression. Without continuous validation, security posture decays silently.
This is not a tooling failure. It is a lifecycle failure.
Continuous Pentesting Requires Change Intelligence
True continuous penetration testing does not mean “running the same test more often.” That simply creates more noise.
What it requires is change-aware security validation—the ability to understand when something changed, what changed, and whether that change introduced new exploitability.
This is where Snapsec Change Management fundamentally shifts how penetration testing works.
How Snapsec Change Management Modernizes Penetration Testing
Snapsec Change Management is designed to sit at the intersection of infrastructure evolution and security validation. Instead of treating penetration testing as a standalone activity, it embeds offensive security logic directly into the lifecycle of change.
Continuous Visibility Into What Changed

Snapsec continuously tracks changes across the external and internal attack surface, including:
- New or modified assets
- Configuration drift
- Service exposure changes
- Authentication and access behavior changes
- Third-party and vendor-driven exposure
This creates a live baseline of the organization’s security posture. Every deviation from that baseline is recorded, contextualized, and evaluated.
Penetration testing no longer starts with “What should we test?” It starts with “What changes need to be tested?”
Change-Triggered Attack Validation

Instead of running broad, periodic penetration tests, Snapsec uses change events as triggers for targeted security validation.
When exposure changes in a way that could introduce risk, Snapsec:
- Identifies affected attack paths
- Re-evaluates exploitability in context
- Flags regression risks where prior fixes may have been undone
- Highlights changes that materially increase attacker opportunity
This turns penetration testing into a continuous feedback loop rather than a scheduled exercise.
Security testing becomes selective, timely, and relevant.
From Reports to Ongoing Risk Signals

Traditional penetration tests end with a report. That report immediately begins to age.
Snapsec replaces static reporting with persistent risk signals. Findings are continuously re-evaluated as the environment evolves. A vulnerability that was low risk yesterday may become critical tomorrow due to an unrelated infrastructure change.
This enables security teams to:
- Track risk trajectories over time
- Understand which fixes remain effective
- Detect when risk quietly returns
- Prioritize based on real exploitability, not historical severity
Penetration testing becomes a living system, not a document.
Operational Impact for Security and Engineering Teams
By anchoring penetration testing to change management, Snapsec removes friction between Security and Engineering.
Security teams gain:
- Continuous validation without constant manual testing
- Evidence-based prioritization tied to real exposure
- Early detection of regressions before attackers exploit them
Engineering teams gain:
- Clear, contextual findings tied to specific changes
- Faster feedback loops
- Fewer disruptive, last-minute security escalations
Leadership gains:
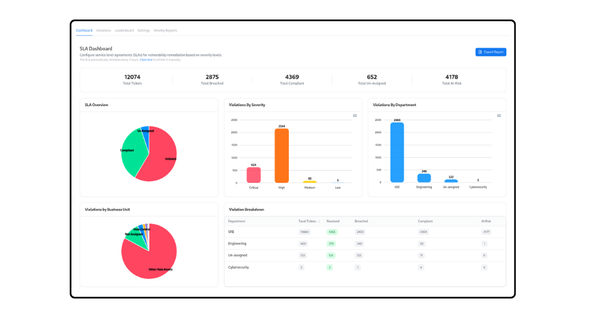
- A measurable view of risk over time
- Confidence that security posture is continuously validated
- Reduced dependence on outdated assurance models
Why This Matters More Than Ever
Attackers do not wait for penetration tests. They monitor change. They look for newly exposed assets, misconfigurations, and regression windows created by routine deployments.
A security strategy that only tests periodically is one step behind by design.
Snapsec Change Management aligns penetration testing with how attackers actually operate, by focusing on change, timing, and opportunity rather than static checklists.
Redefining Penetration Testing as a Capability, Not a Service
One-time penetration testing made sense when infrastructure was static and release cycles were slow. That world no longer exists.
In modern environments, security assurance must be continuous, contextual, and responsive to change. Snapsec does not replace penetration testing, it evolves it into an ongoing risk validation process embedded directly into the organization’s operational reality.
When penetration testing is driven by change, security stops chasing the past and starts defending the present.
That is the shift Snapsec Change Management delivers.