How Snapsec Unifies and Governs the Modern Digital Footprint
Modern security programs don’t fail because of missing scanners.
They fail because of fragmented visibility.
Domains live in one tool.APIs in another.IP ranges in spreadsheets.Certificates in someone’s inbox.Repositories in DevOps.Cloud buckets in yet another dashboard.
Security teams think they have visibility.
In reality, they have silos.
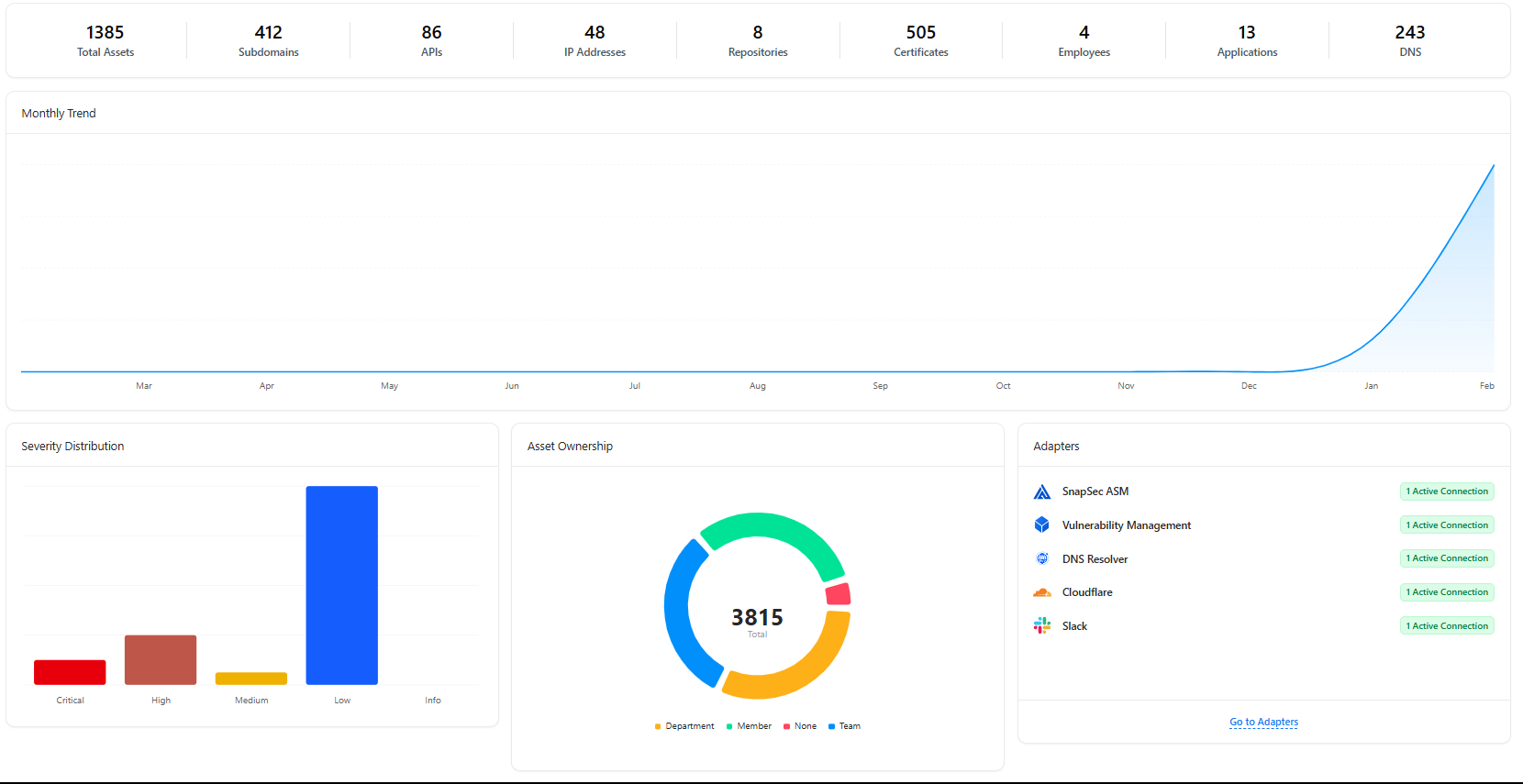
Snapsec Asset Inventory Management eliminates this fragmentation by centralizing every digital asset into a single, continuously updated, ownership-driven inventory layer.
1. A True Unified Asset View (Not Just a List)
Most organizations maintain separate inventories for:
- Subdomains
- APIs
- IP addresses
- SSL certificates
- Code repositories
- Applications
- Technologies
- Employee-linked assets
Snapsec consolidates all of them into one structured, searchable asset layer.
From a single dashboard, teams can see:
- Total asset footprint
- Distribution across categories
- Ownership mapping
- Associated vulnerabilities
- Detection timestamps
This isn’t static documentation. It’s a living inventory.
2. Subdomain & External Surface Visibility
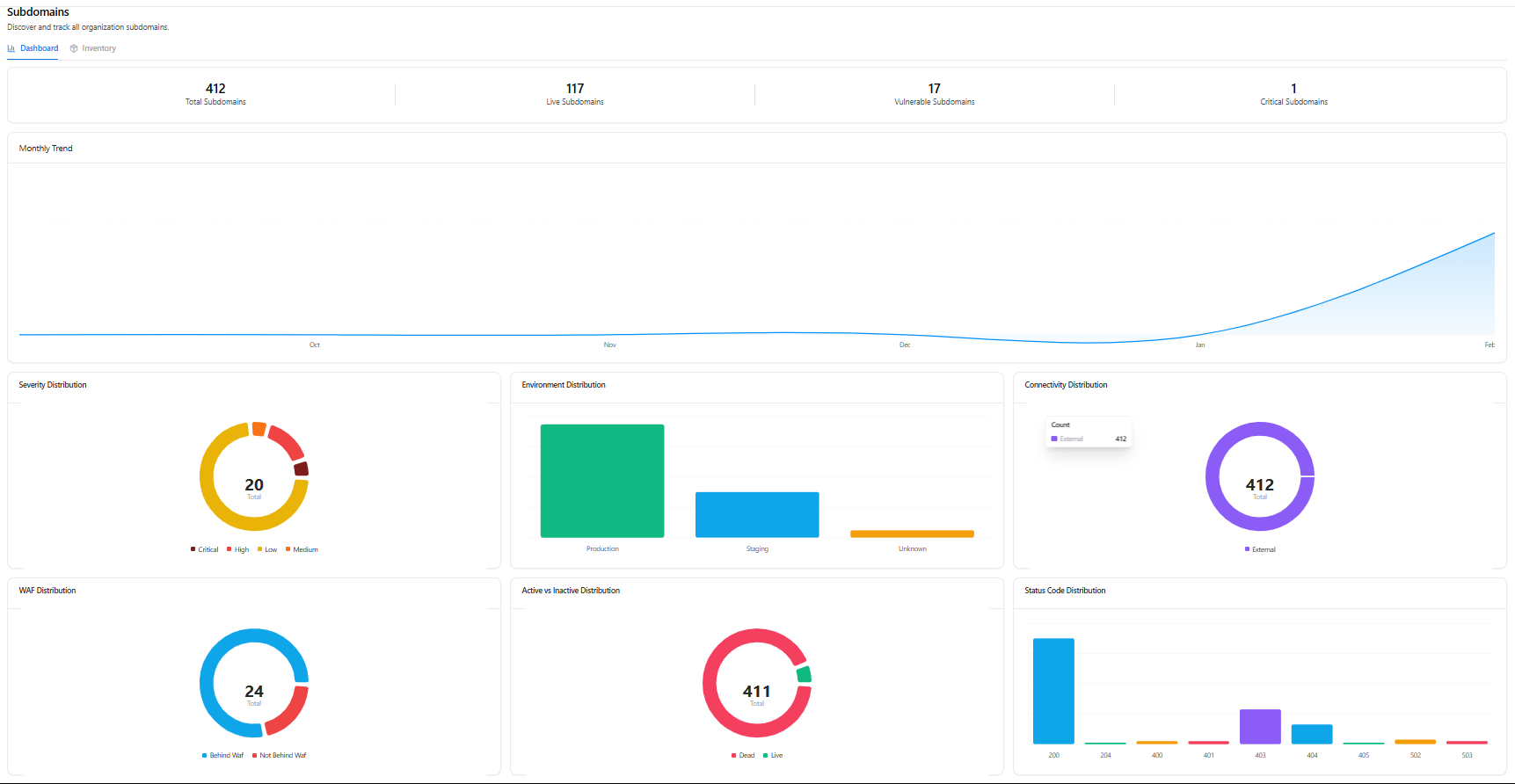
Subdomains are one of the most common blind spots in enterprise security.
Marketing launches new campaigns.Dev teams deploy staging environments.Legacy systems remain forgotten.
Snapsec continuously tracks:
- Total subdomains
- Live vs inactive assets
- Vulnerable subdomains
- Production vs staging distribution
- External exposure status
- WAF protection status
- HTTP response behavior
Security teams immediately understand:
- Which subdomains are public
- Which are exposed without protection
- Which are introducing risk
No manual DNS reviews required.
3. API & IP Intelligence with Risk Context
APIs are expanding faster than traditional infrastructure.
IP ranges shift across cloud providers.Endpoints change without centralized documentation.
Snapsec provides:
API Inventory:
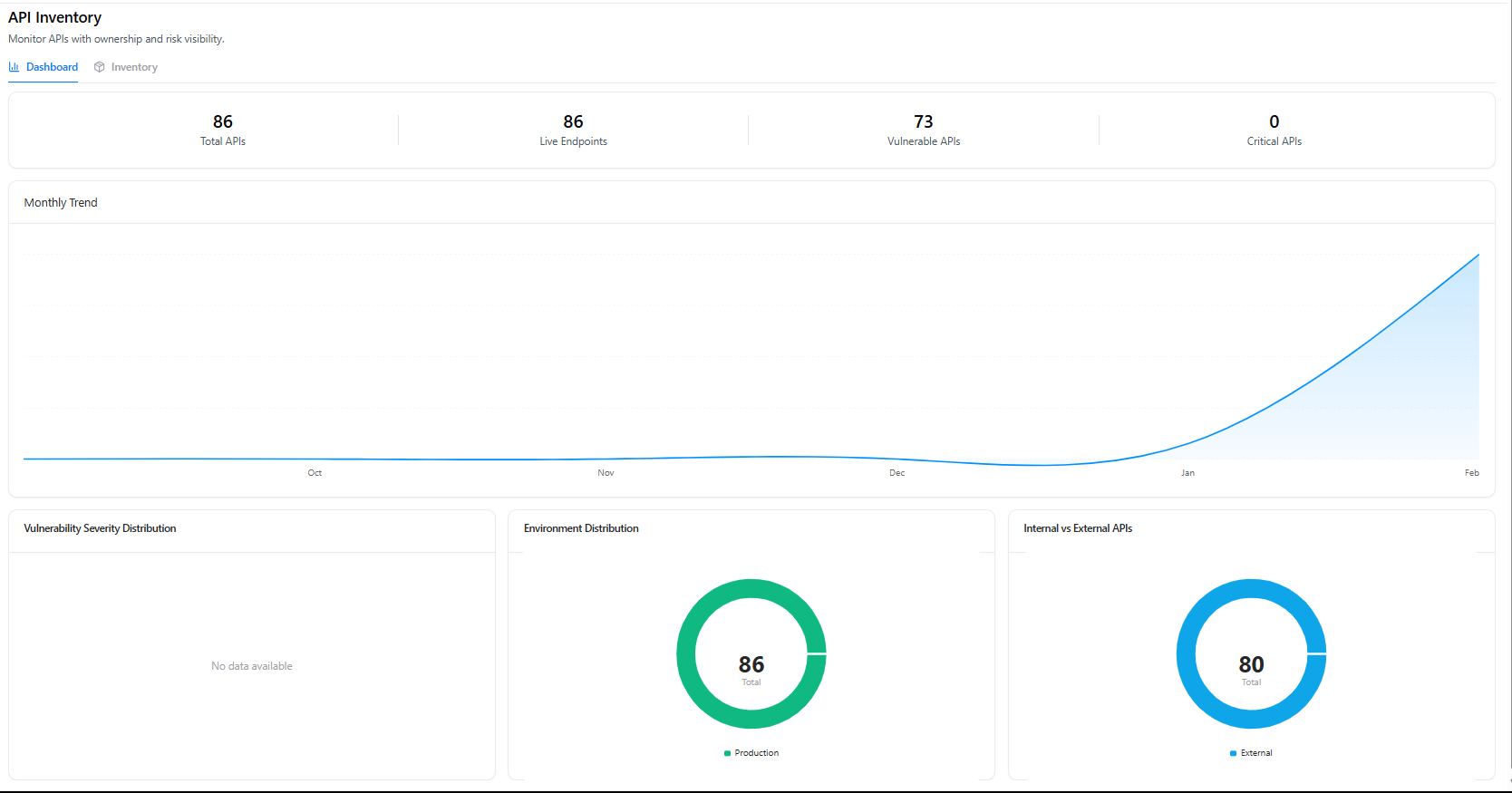
- Total APIs and live endpoints
- Vulnerable API tracking
- Internal vs external exposure
- Environment classification
IP Inventory:
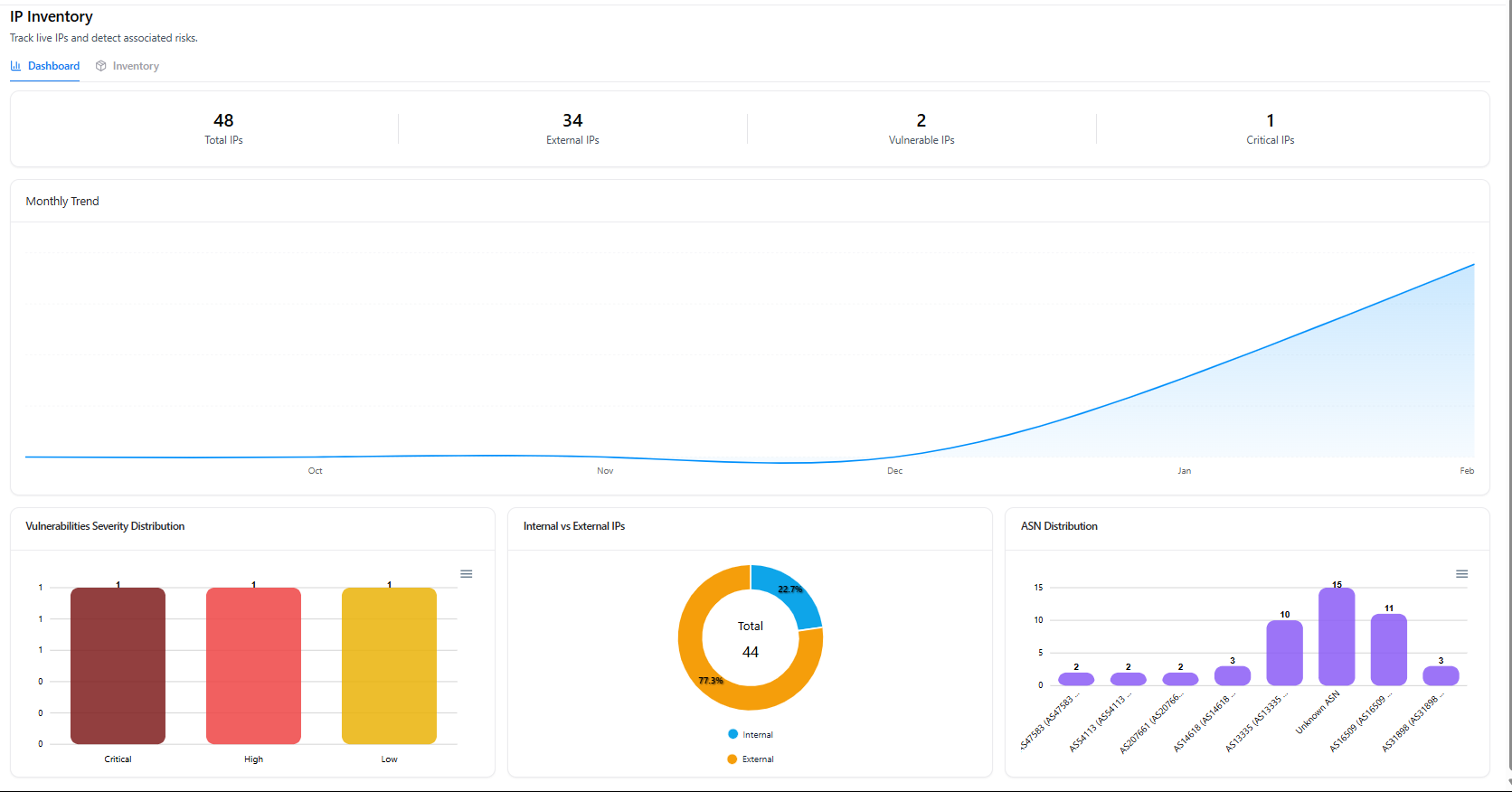
- Total IP footprint
- External vs internal distribution
- ASN mapping
- Vulnerability severity breakdown
Instead of reacting to API exposure after incidents, teams see exposure trends in real time.
This transforms API and IP governance from reactive to proactive.
4. DNS & Certificate Governance
DNS and certificates are often operationally owned but rarely security-governed.
Snapsec centralizes:
DNS Management:
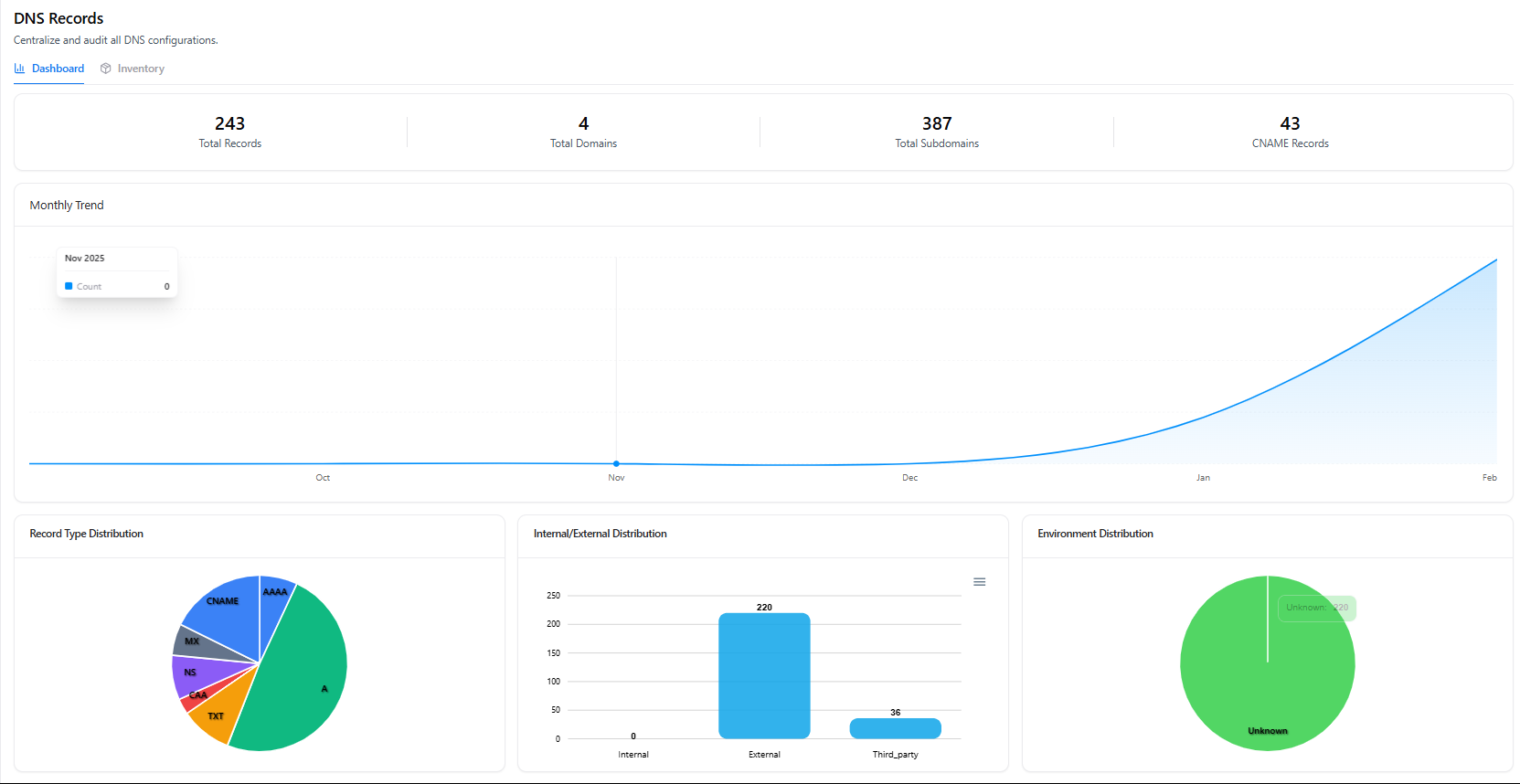
- Record type distribution (A, CNAME, TXT, MX, etc.)
- Internal vs external record mapping
- Domain & subdomain visibility
- Third-party linkage
SSL Certificate Oversight:

- Total certificates
- Expired certificates
- Expiring soon
- Valid distribution
- Certificate authority mapping
This prevents:
- Certificate expiration outages
- Forgotten DNS records
- Shadow third-party routing
Governance becomes measurable instead of assumed.
5. Code, Applications & Technology Stack Mapping
Security does not stop at infrastructure.
Snapsec maps:
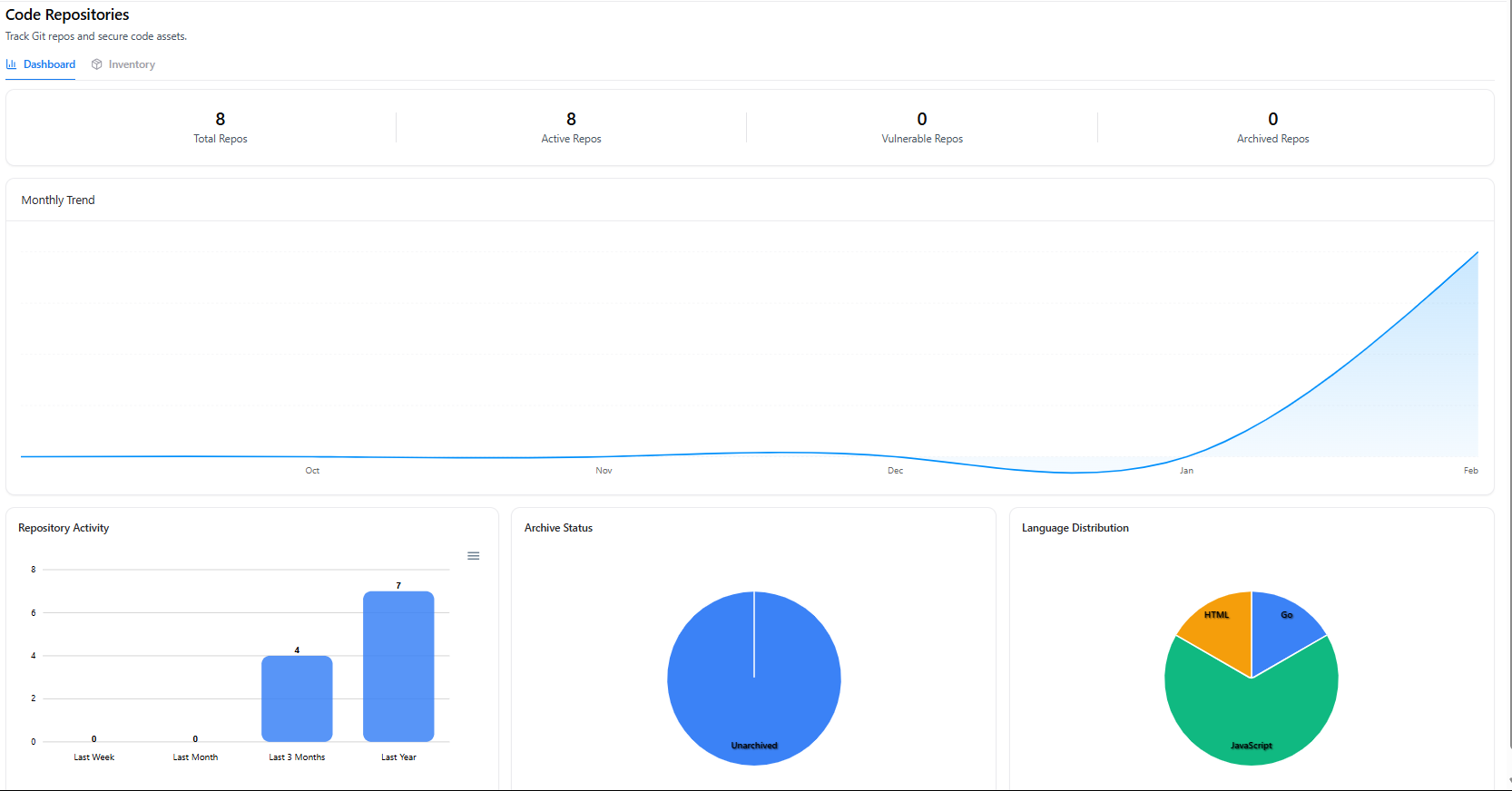
- Git repositories
- Repository activity
- Language distribution
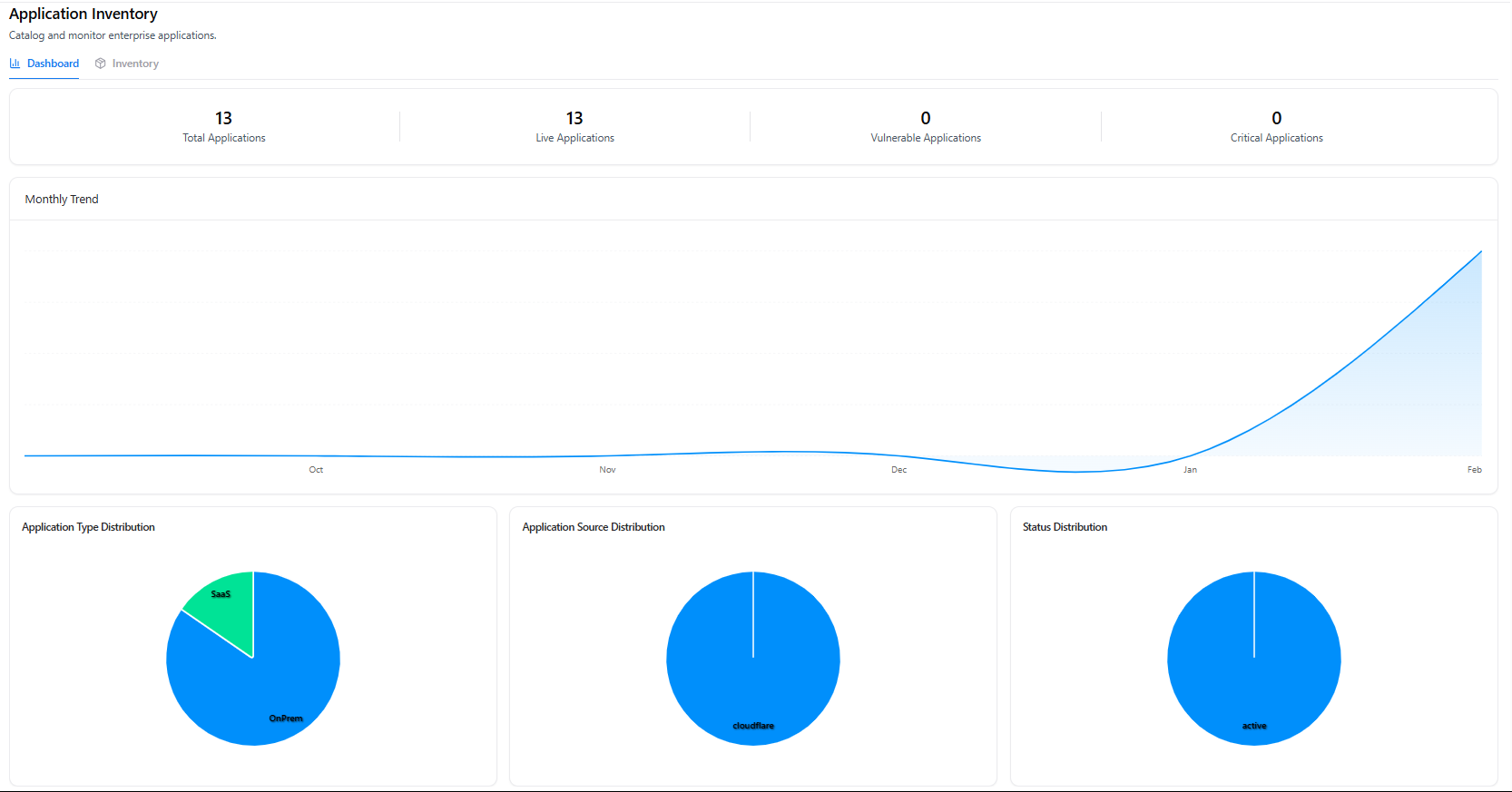
- Application types (SaaS vs On-Prem)
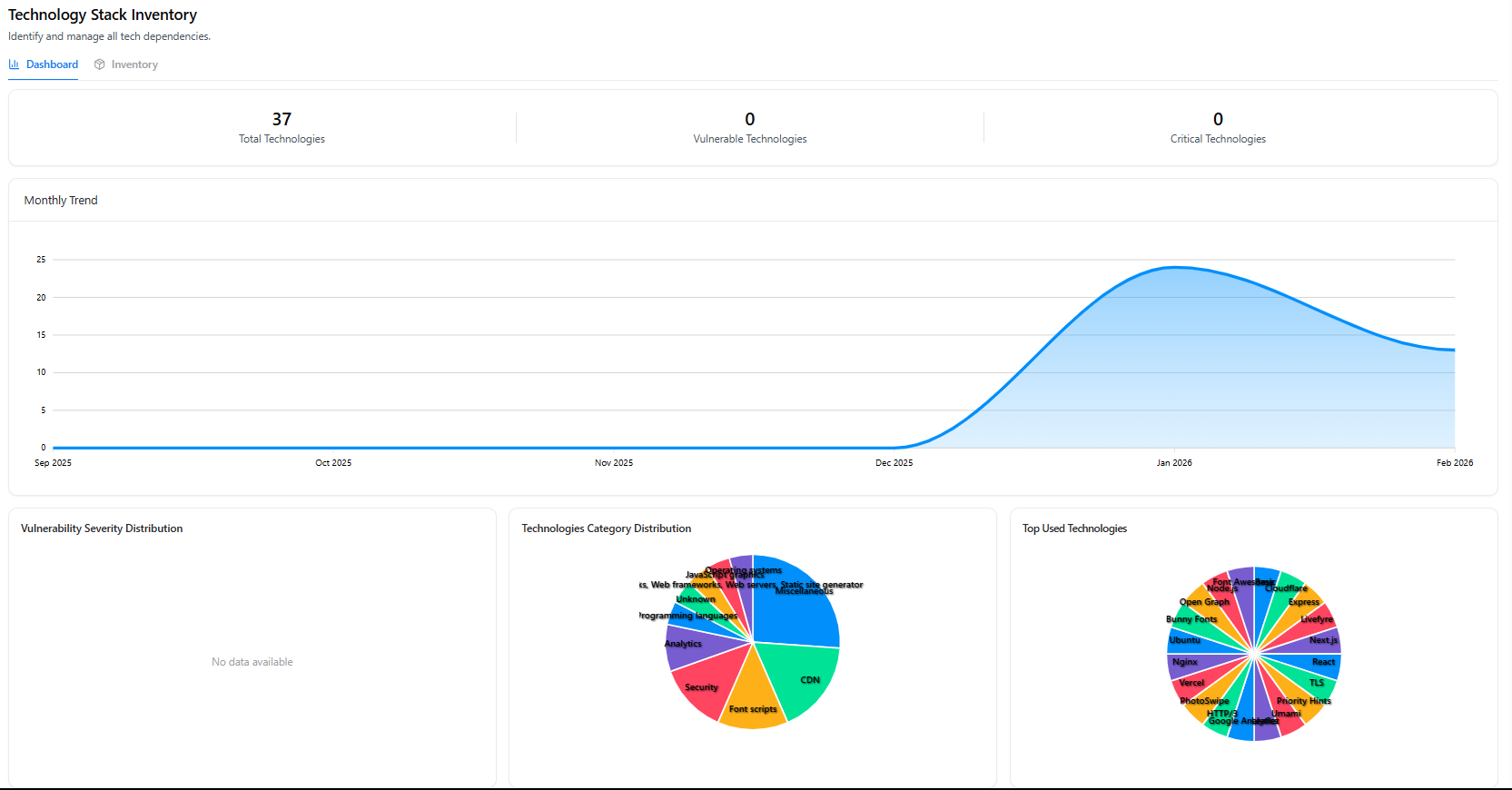
- Technology stack dependencies
- CDN, analytics, security tech usage
This allows teams to answer:
- What technologies are we dependent on?
- Which applications are externally exposed?
- Which repositories are active and monitored?
- Where is business-critical infrastructure hosted?
Asset inventory becomes context-aware, not just enumerated.
6. Employee & Workstation Asset Mapping
Attack surfaces increasingly originate from identity and endpoint exposure.
Snapsec links:
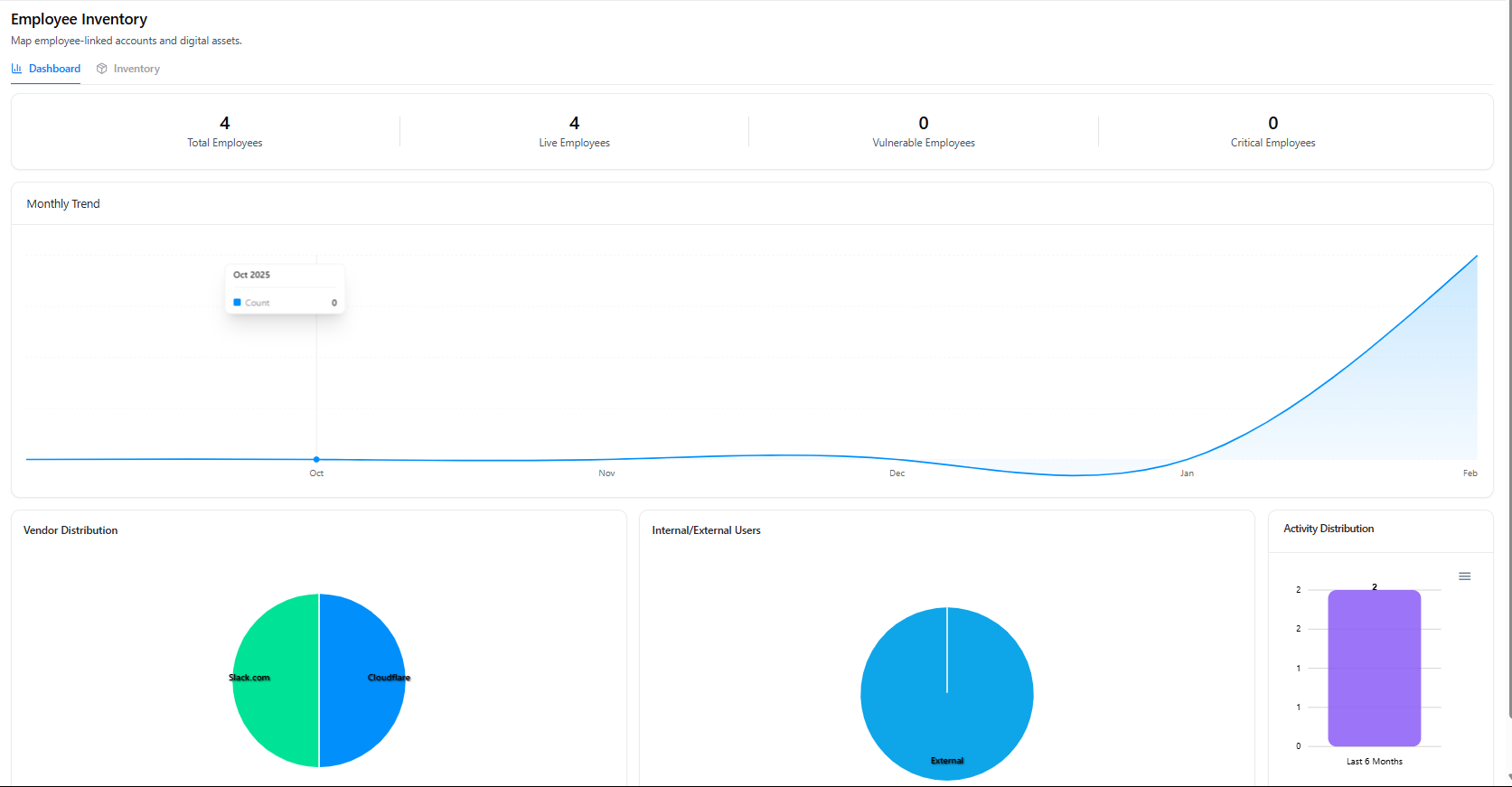
- Employees to digital assets
- Vendor-linked access
- Internal vs external users
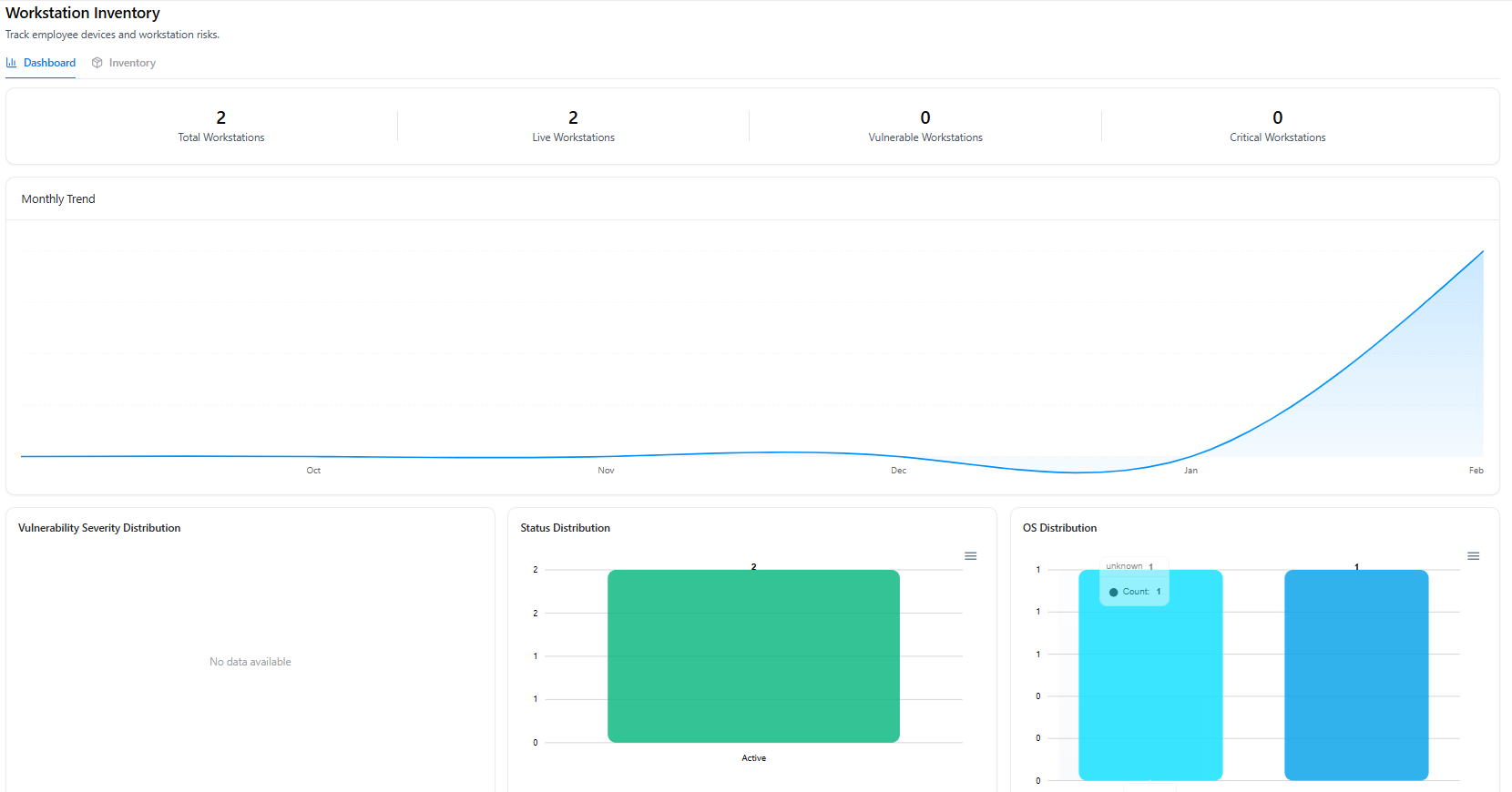
- Workstation status
- OS distribution
- Endpoint activity
This connects identity to infrastructure.
Ownership stops being theoretical.
7. Business Unit Mapping & Accountability
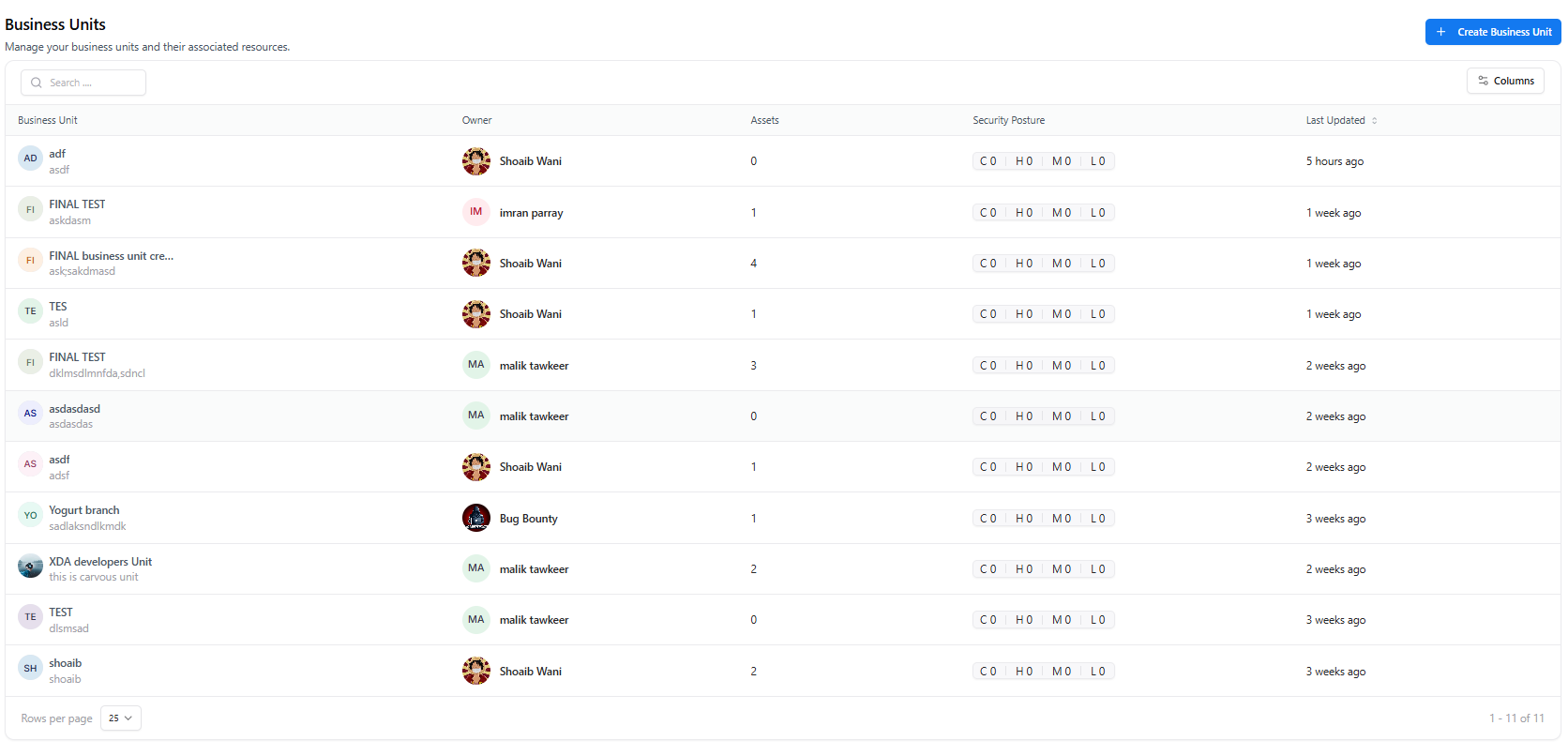
Visibility without ownership creates noise.
Snapsec maps assets to:
- Business units
- Designated owners
- Security posture summaries
- Vulnerability severity counts
This ensures:
- Every asset has accountable oversight
- Exposure can be traced to responsible teams
- Risk is measurable at the organizational level
Asset management becomes enforceable governance.
The Operational Gap Snapsec Closes
Traditional asset inventory systems fail because:
- They rely on manual updates
- They break during cloud scale
- They are not vulnerability-aware
- They do not map ownership
- They cannot unify multiple asset categories
Snapsec replaces fragmented asset tracking with:
- Continuous discovery
- Cross-category normalization
- Real-time trend monitoring
- Ownership mapping
- Vulnerability context
- Governance visibility
This is not an asset list.
It is a structured, continuously maintained digital asset intelligence layer.
Why This Matters for Security Leadership
When asset inventory is fragmented:
- Shadow IT grows silently
- APIs expand without tracking
- Certificates expire unnoticed
- DNS misconfigurations go undetected
- Ownership becomes unclear
- Risk reporting becomes inaccurate
When asset inventory is unified:
- Exposure reflects reality
- Risk scoring becomes reliable
- Accountability becomes enforceable
- Governance becomes measurable
Security stops operating on assumptions.
It operates on structured visibility.
Explore a Live Demo
Stop managing assets across spreadsheets and disconnected tools.
See how Snapsec centralizes your entire digital footprint into one governed, continuously updated inventory system.