Continuous Attack Surface Monitoring with Snapsec
Most organizations conduct security reviews on a schedule.
Quarterly audits. Annual penetration tests. Periodic vulnerability scans.
On paper, this creates the appearance of a well-governed security program.
In reality, the attack surface does not follow review cycles.
New infrastructure is deployed daily.
Subdomains are created during product launches.
Cloud resources appear and disappear within hours.
APIs are exposed during development cycles.
Certificates expire or get replaced without centralized visibility.
Between two scheduled security reviews, the environment may have changed dozens of times.
Attackers do not wait for the next audit window.
They monitor continuously.
This is the gap Snapsec closes.
Snapsec continuously tracks the organization’s digital footprint and identifies exposure changes the moment they occur, allowing security teams to detect attack surface drift in real time instead of discovering it months later.
1. Real-Time Asset Discovery Across the Attack Surface
Security visibility begins with discovery.
Snapsec continuously monitors the organization’s external surface and detects new assets as they appear across multiple categories, including:
- Subdomains
- APIs
- IP addresses
- DNS records
- SSL certificates
- Applications
- Code repositories
- Cloud-linked infrastructure
Instead of relying on manually maintained inventories, Snapsec automatically builds and updates a structured asset inventory.
When a new asset becomes externally visible, it is immediately recorded and classified.
Security teams no longer depend on periodic discovery scans to understand what exists.
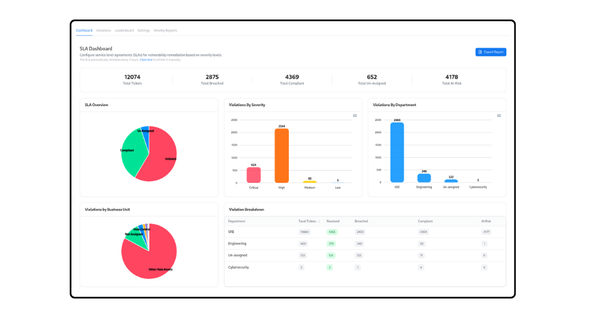
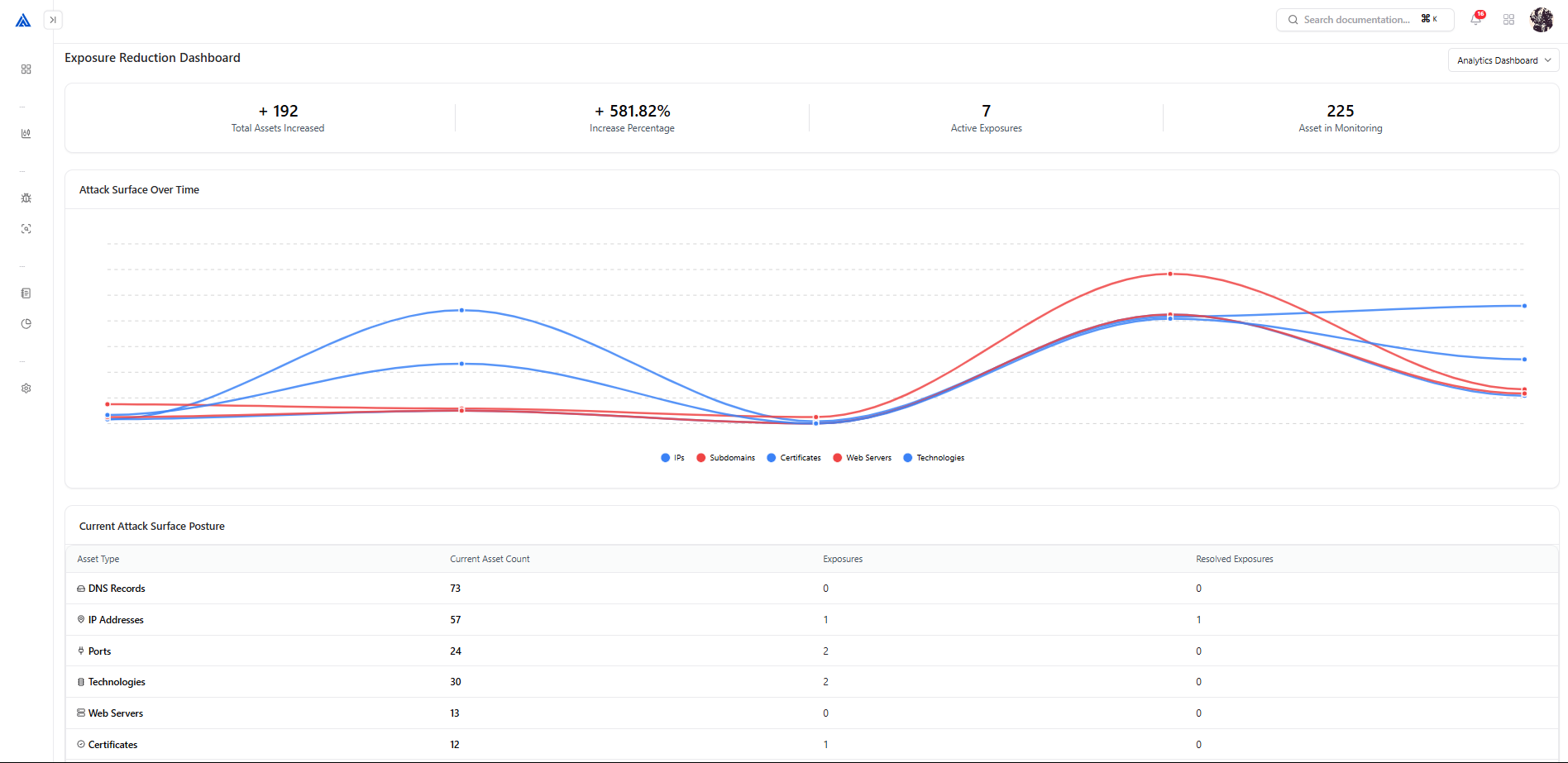
2. Detecting Attack Surface Drift
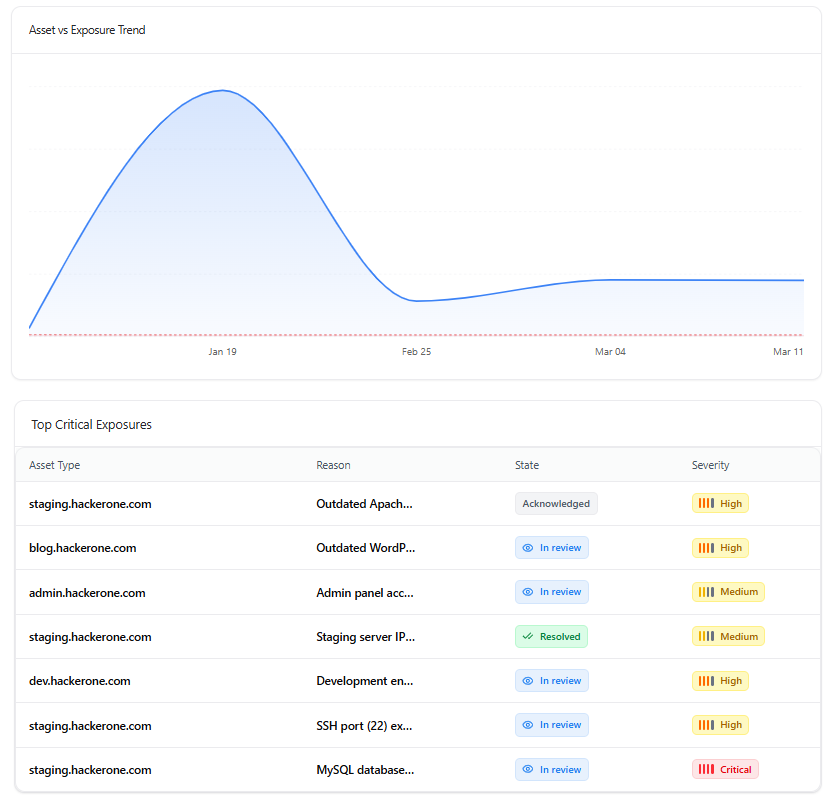
Attack surface drift occurs when an organization’s external exposure changes without security oversight.
These changes rarely happen during scheduled security reviews. They happen during everyday operations.
A staging server is left publicly accessible.
A development endpoint is exposed.
A legacy system remains reachable on the internet.
An outdated service continues running unnoticed.
Over time, these small changes expand the organization’s external attack surface.
Snapsec continuously monitors these shifts and highlights them through real-time exposure trends.
Security teams can immediately see:
- Changes in asset exposure over time
- Newly detected risky services
- Critical vulnerabilities tied to exposed assets
- Severity levels associated with each exposure
Instead of waiting for the next audit or penetration test to reveal these issues, Snapsec surfaces them the moment they appear.
This allows teams to investigate new exposures quickly, assign ownership, and remediate risk before it becomes an entry point for attackers.
Continuous visibility turns attack surface drift from a delayed discovery problem into a real-time operational signal.
3. Immediate Visibility into Newly Exposed APIs and Services
APIs are one of the fastest-growing components of modern infrastructure.
New endpoints can appear during:
- Microservice deployments
- Feature releases
- Integration testing
- Internal service exposure
Without continuous monitoring, APIs can become externally accessible without security review.
Snapsec continuously tracks API exposure and provides immediate visibility into:
- Newly detected APIs
- External vs internal endpoints
- Environment classification
- Associated vulnerabilities
This ensures that exposed APIs are identified early, before they become an attacker’s entry point.
4. IP and Infrastructure Changes in Real Time
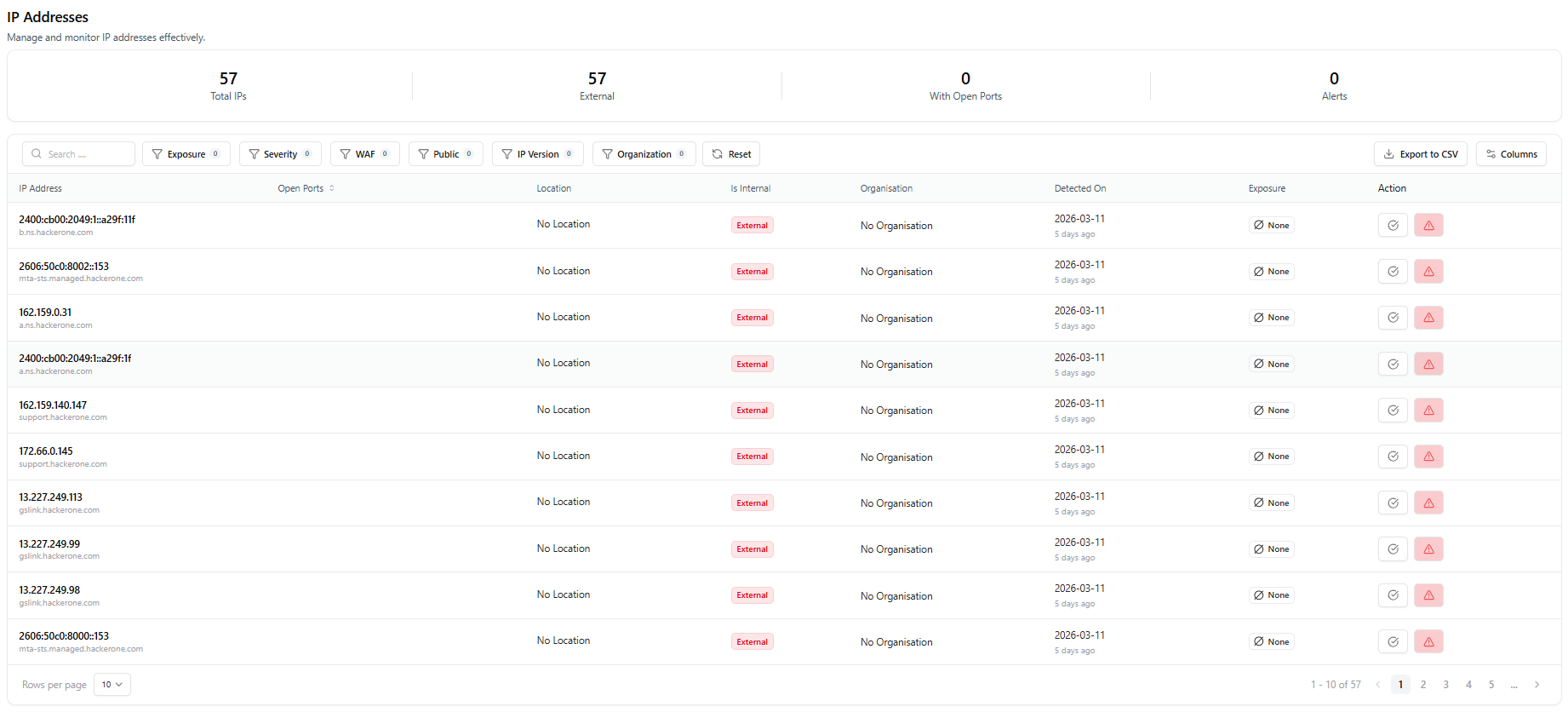
Cloud infrastructure changes constantly.
New instances are deployed. Services move between providers. IP addresses are reassigned or exposed publicly.
These changes can quietly expand the organization’s external attack surface.
Snapsec continuously monitors IP infrastructure and provides real-time visibility into:
- Newly discovered IP addresses
- Internal vs external infrastructure exposure
- Open ports associated with IPs
- Organization and hosting information
- Detection timestamps for newly observed infrastructure
With this visibility, security teams can quickly identify when new infrastructure appears or when existing systems become externally accessible.
Instead of discovering exposed infrastructure during periodic reviews, Snapsec surfaces these changes immediately—allowing teams to investigate potential risk as it emerges.
5. DNS and Certificate Changes That Signal Exposure
DNS changes are often the earliest signal that new infrastructure has gone live.
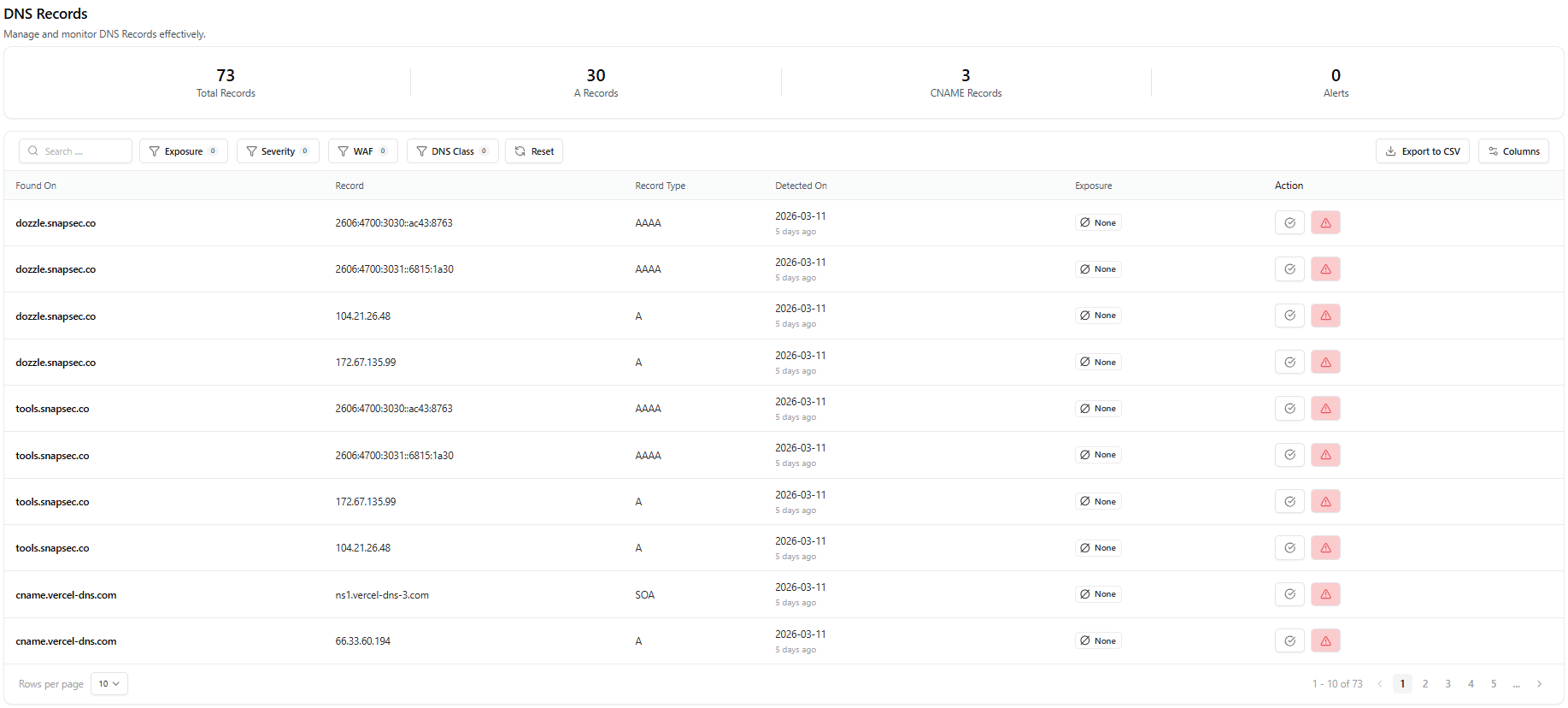
When a new DNS record appears, it may indicate a staging environment, development endpoint, or third-party service connected to the organization’s domain. Without continuous monitoring, these changes can introduce exposure that security teams may not detect until much later.
Snapsec continuously tracks DNS activity across the organization’s domains, providing visibility into:
- Newly created DNS records
- Changes to existing records
- Record types such as A, AAAA, CNAME, and SOA
- Domain and subdomain relationships
SSL certificates provide another key indicator of external exposure. When a new certificate is issued, it often means a service has been deployed publicly and is accepting encrypted connections.
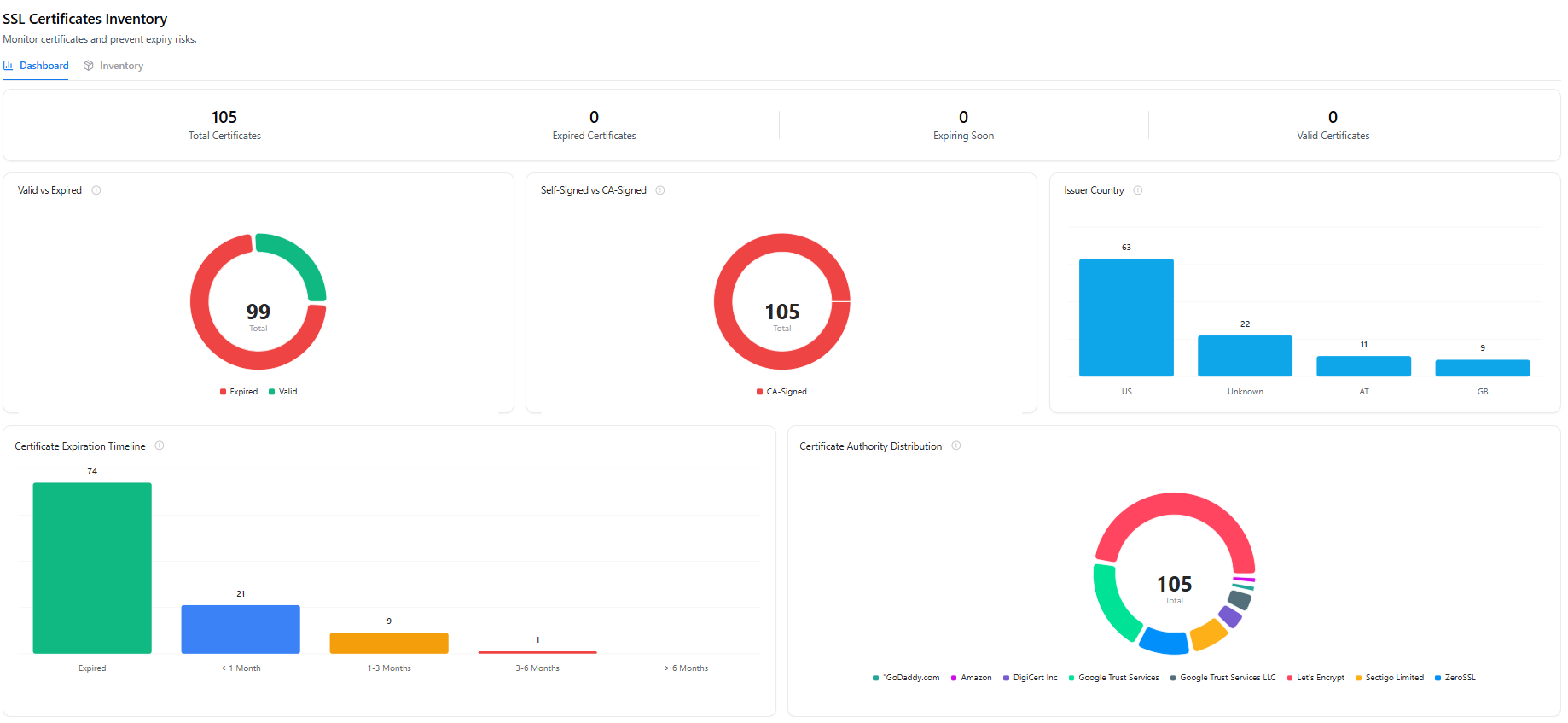
Snapsec monitors certificate activity including:
- Certificate issuance and expiration
- Valid and expired certificates
- Certificate authority distribution
- Certificate expiration timelines
By tracking DNS and certificate activity together, Snapsec helps security teams quickly identify when new infrastructure becomes publicly accessible and investigate potential exposure immediately.
6. Ownership Mapping for Newly Discovered Assets
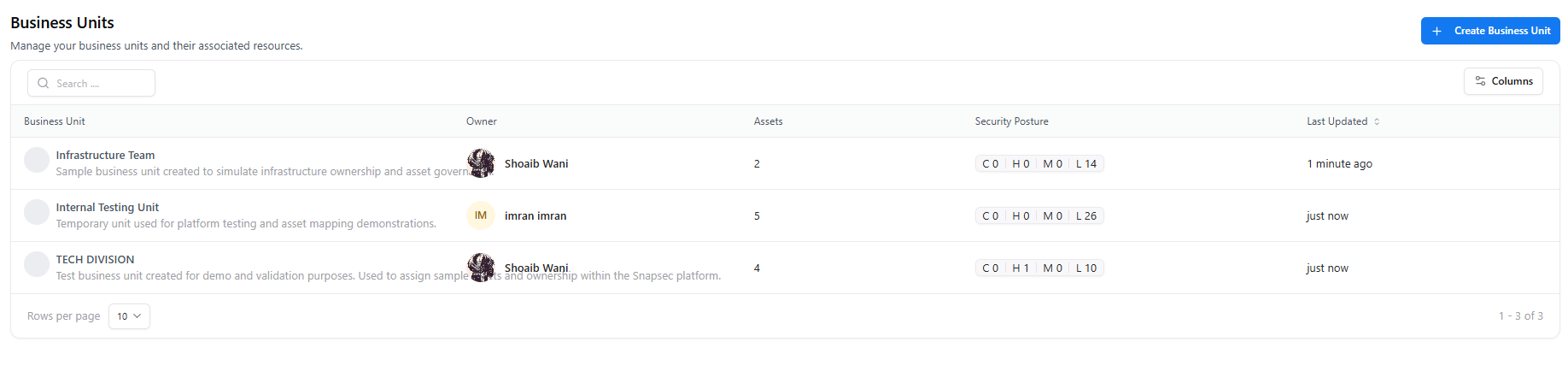
Discovery alone is not enough.
Every asset needs clear ownership.
Snapsec connects discovered assets directly to business units and responsible teams, ensuring that exposure is always tied to an accountable owner.
Security teams can view:
- Business units responsible for assets
- Assigned asset owners
- Number of assets under each unit
- Security posture across assets
- Recent updates to ownership or asset mappings
When a new asset appears, teams can immediately determine:
- Which business unit owns it
- Who is responsible for remediation
- How the asset affects the unit’s security posture
Instead of chasing infrastructure teams across departments, security teams have immediate visibility into who owns what.
Ownership turns asset discovery into enforceable governance.
Why Continuous Visibility Matters
When security reviews are periodic:
- New assets remain unnoticed
- APIs become externally accessible without review
- Infrastructure changes introduce hidden exposure
- DNS records point to unintended destinations
- Ownership becomes unclear
By the time these issues appear in an audit or pentest report, they may have existed for months.
Continuous monitoring eliminates this delay.
Snapsec ensures that security teams see the attack surface as it evolves — not after the fact.
The Operational Advantage
Snapsec replaces periodic visibility with continuous awareness by providing:
- Real-time asset discovery
- Attack surface drift detection
- API and infrastructure exposure monitoring
- DNS and certificate change tracking
- Ownership and governance mapping
Security stops operating on snapshots.
It operates on continuous intelligence.