The Assets That Keep CISOs Awake at Night

In modern enterprises, asset growth outpaces visibility. Infrastructure expands across multiple cloud providers, DNS zones multiply, APIs are deployed rapidly, and acquisitions introduce entirely new technology stacks. While security teams invest heavily in vulnerability detection, many organizations still depend on static asset inventories to define their security scope.
Manual inventories introduce risk. They rely on periodic updates, internal reporting, and human accuracy. In fast-moving environments, this approach cannot keep pace with asset creation and infrastructure change. The result is incomplete visibility into the organization’s true external exposure.
For CISOs, this gap creates uncertainty. Security programs may appear mature, but if the underlying asset inventory is incomplete, the foundation of the program is compromised.
The Operational Gap in Asset Governance
External assets emerge from multiple sources:
- Cloud workloads provisioned by development teams
- New domains registered by marketing or regional teams
- Public IP ranges added during expansion
- APIs deployed through CI/CD pipelines
- Infrastructure inherited through acquisitions
In many cases, these assets are not formally registered with security teams. Over time, asset visibility drifts away from reality. What exists externally no longer aligns with what the organization believes exists.
Attackers, however, do not rely on internal spreadsheets. They discover what is publicly reachable. The difference between assumed visibility and actual exposure is where risk accumulates.
How Snapsec Solves It
Snapsec transforms asset management from a documentation process into a continuous, automated exposure discovery and normalization system.
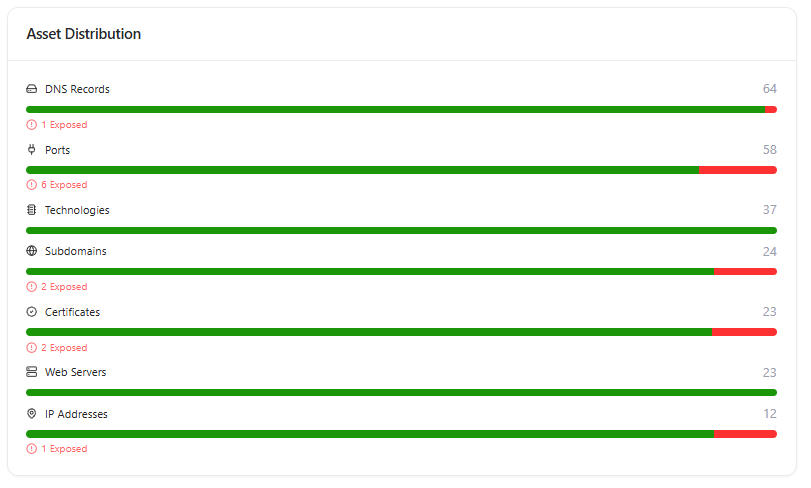
Continuous External Asset Discovery
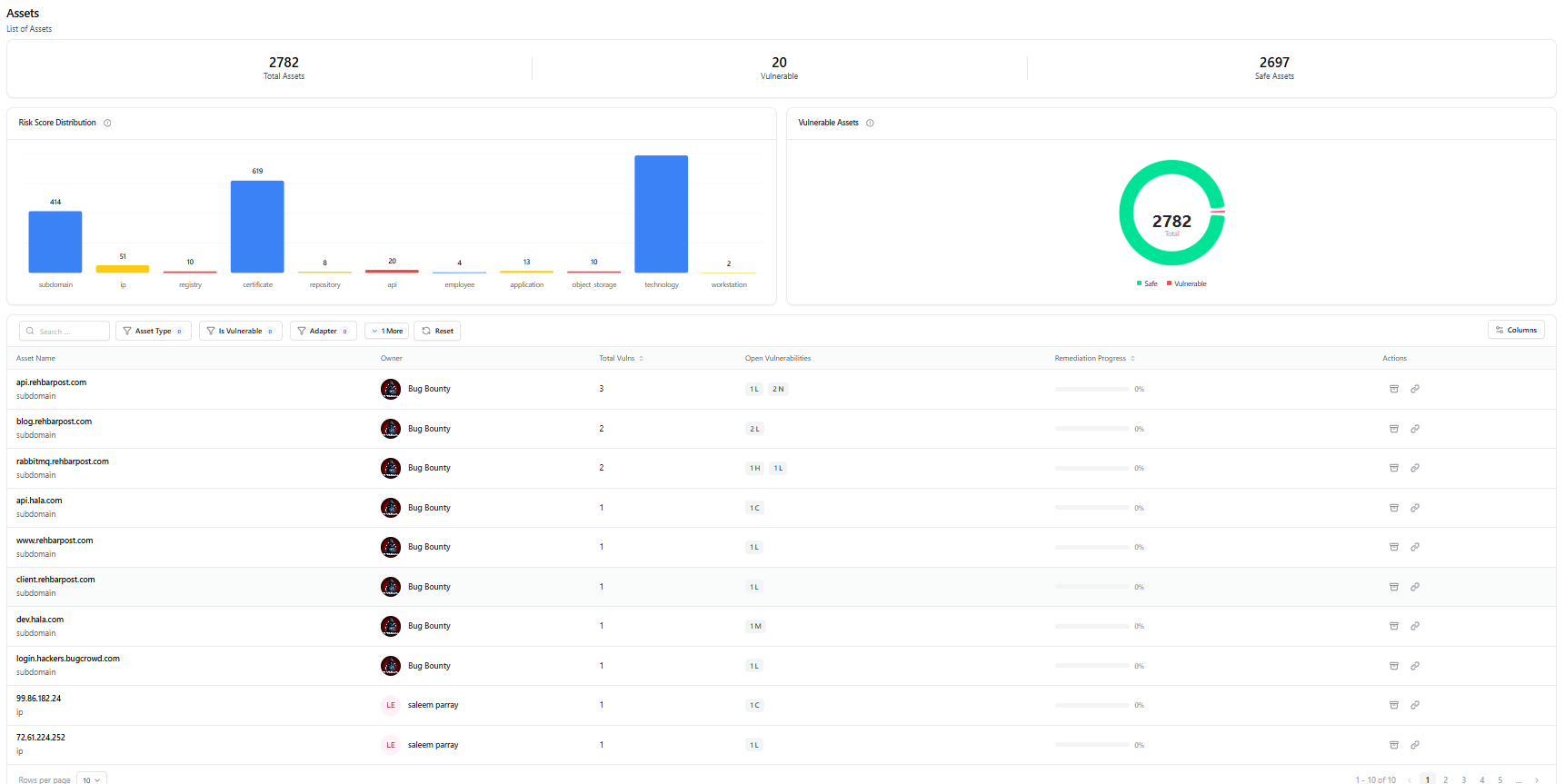
Snapsec continuously identifies and maps external-facing assets across domains, subdomains, IP ranges, cloud services, exposed ports, and publicly accessible APIs. Discovery is automated and ongoing, ensuring that newly created or externally exposed assets are incorporated into the inventory without manual intervention.
This enables security teams to maintain alignment between real-world exposure and internal visibility.
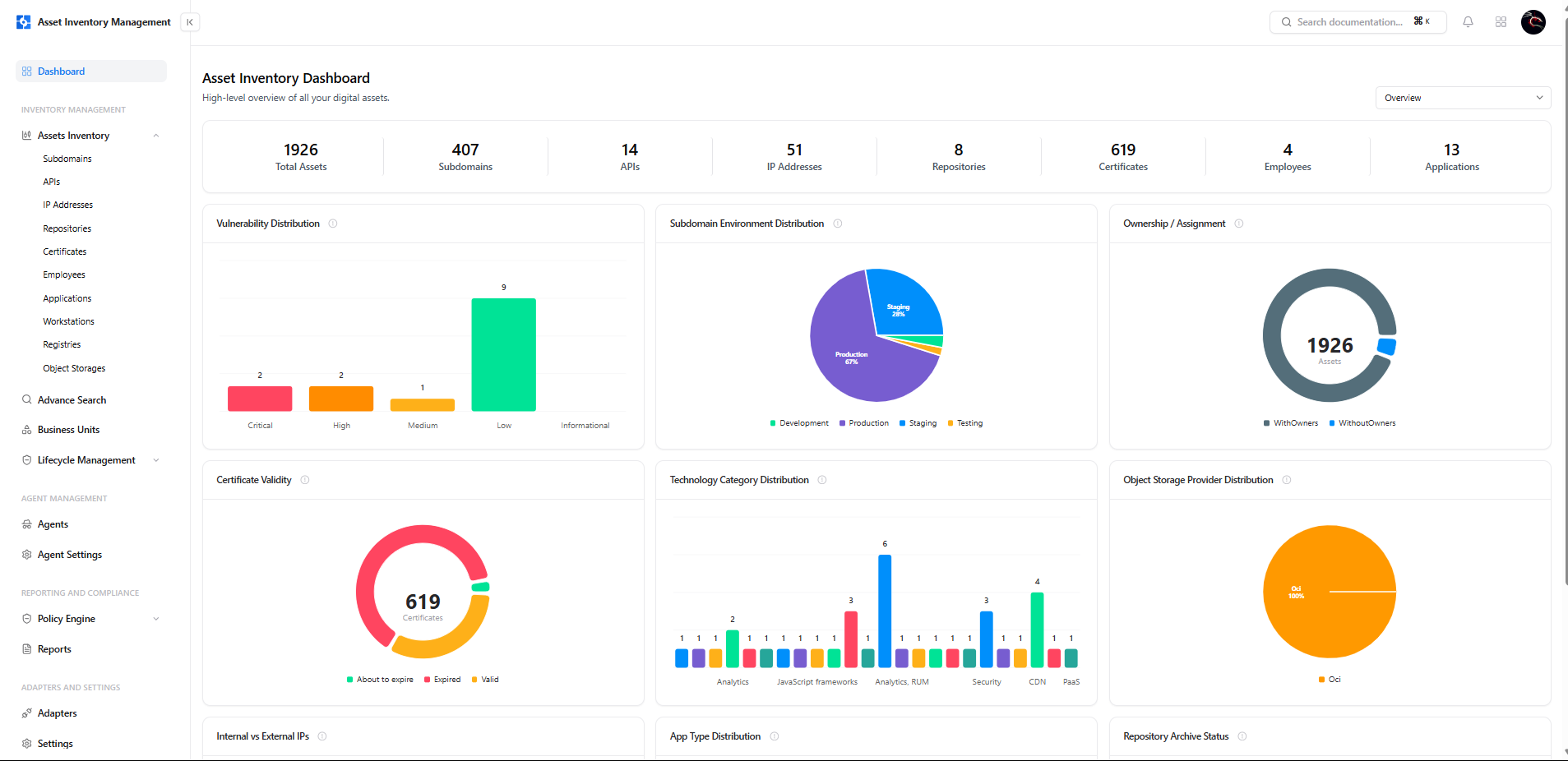
Centralized Asset Inventory Normalization
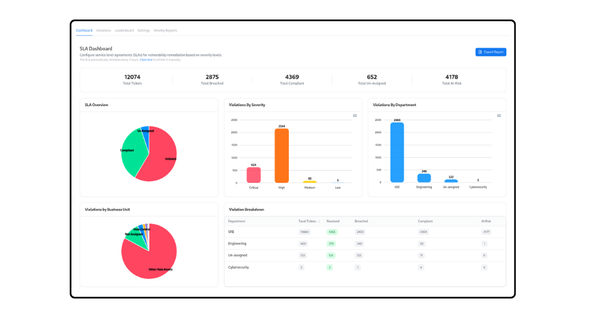
Discovery alone does not provide governance. Snapsec consolidates discovered assets into a unified Asset Inventory Management (AIM) framework where assets are structured, categorized, and normalized.
Each asset can be mapped to business units, tagged by environment, associated with ownership, and correlated with related risk signals. This provides a centralized source of truth that reflects the organization’s current external footprint.
Integration of Acquisitions and Subsidiaries
Acquisitions often introduce unmanaged domains, inherited infrastructure, and differing security standards. Snapsec automatically incorporates newly associated domains and IP ranges into the centralized inventory, ensuring that expansion events do not create unmanaged exposure.
This reduces the time between acquisition and visibility, allowing governance to extend across newly integrated entities without waiting for manual reconciliation.
Correlation Across Cloud, DNS, IPs, and APIs
Snapsec does not treat assets as isolated records. Each discovered asset is enriched with contextual data, including open services, SSL certificates, exposed technologies, and linked vulnerabilities. This provides a comprehensive view of both existence and exposure.
Security teams can assess risk posture directly from the inventory, without shifting between multiple disconnected tools.
Continuous Monitoring Instead of Periodic Audits
Traditional asset audits occur at defined intervals. In contrast, infrastructure changes continuously. Snapsec maintains a live inventory model that reflects changes as they occur, reducing the lag between asset creation and security awareness.
This approach ensures that visibility remains aligned with operational reality rather than audit cycles.
A Structured Asset Governance Model
From discovery and normalization to ownership mapping and risk correlation, Snapsec establishes a closed-loop governance framework for external assets.
Organizations benefit from:
- Automated discovery across cloud, DNS, IP, and API environments
- Normalized and structured asset inventory
- Ownership attribution and business mapping
- Continuous monitoring of exposure changes
- Direct correlation between assets and vulnerabilities
Asset management becomes an active governance function rather than a static documentation requirement.
Why This Matters for CISOs
Enterprise security strategies depend on accurate scope definition. If the asset inventory is incomplete, every downstream control operates on partial information.
By maintaining continuous visibility into external assets and normalizing them into a centralized governance framework, Snapsec strengthens the foundation upon which vulnerability management, threat modeling, and remediation programs operate.