Why SAMA-Compliant Vulnerability Management Fails in Real Life

SAMA sets strict regulatory expectations through frameworks like its Cyber Security Framework, requiring organizations to maintain full visibility of assets, continuously manage vulnerabilities, and enforce clear remediation timelines. The approach is structured, risk-driven, and heavily focused on accountability at every level.
Organizations are expected to do a few key things well. They need to know all their assets, scan them regularly, classify vulnerabilities, and fix them within defined timelines (SLAs). On paper, this sounds simple. In reality, many teams do not have full visibility of their assets, so some systems never get scanned at all.
At the same time, in real-world environments, things are far more complex than they appear on paper. Vulnerabilities are spread across multiple tools covering cloud, code, infrastructure, and traditional vulnerability management platforms. Each of these tools works in isolation, creating silos of data that are difficult to bring together. There is no single, reliable view of risk, and teams often end up working with partial or outdated information.
The Assumption Behind SAMA That Doesn’t Hold
SAMA’s requirements are logically sound on paper:
- Scan all information assets
- Classify vulnerabilities
- Define remediation timelines (SLAs)
The failure is not in the control itself, but in the static assumption underneath it: that “all information assets” is a known, stable set. In high-velocity environments, it isn’t.
Modern infrastructure is defined by ephemerality. Workloads are spun up and destroyed within CI/CD pipelines in minutes. Decentralized cloud accounts create inconsistent governance boundaries. Configuration drift alters exposure—such as an S3 bucket flipping from private to public—without changing the asset’s identity in a CMDB.
When SAMA says “scan all assets,” most organizations actually execute: “Scan all assets we can currently enumerate.” That distinction is where the catastrophe begins.
The First Gap: Incomplete Asset Catalog
Vulnerability management starts with a dependency that is quietly broken: asset discovery.
The first gap in vulnerability management is an incomplete asset catalog. Everything starts with knowing what you actually own, but in many organizations, this is where things begin to break down. Asset discovery is often treated as a one-time activity instead of a continuous process. As a result, inventories quickly become outdated, missing new systems, cloud resources, and applications that are constantly being added.
When the asset catalog is incomplete, vulnerability management becomes unreliable from the start. Scans only cover what is known, leaving unknown or unmanaged assets completely exposed. This creates a false sense of security, where reports look clean but critical gaps remain hidden. Without a complete and up-to-date view of assets, it becomes almost impossible to manage vulnerabilities effectively or ensure that risks are truly under control.
The Second Gap: Lack of Asset Prioritisation
Even if you somehow enumerate 100% of your assets, you still don’t know what matters. Most VM tools provide CVSS scores and package-level weaknesses, but they provide zero context on reachability.
A "Critical" vulnerability in a library sitting in a dormant container image is functionally zero risk. Conversely, a "Medium" vulnerability on an internet-facing load balancer that allows an attacker to assume a high-privilege IAM role is a business-ending event.
SAMA enforces remediation timelines based on severity, but without reachability context, teams succumb to SLA Exhaustion. They spend 60 hours a week patching isolated "Critical" bugs to satisfy an auditor, while reachable "Medium" findings—the ones that actually facilitate a breach—sit in the backlog because they don't trigger a compliance flag.
The Third Gap: Fragmented Vulnerability Data
Defining an SLA is a governance exercise; enforcing it is an operational nightmare. In a fragmented environment, vulnerabilities originate from siloed tools: network scanners, CSPM platforms, and SAST/DAST pipelines.
SLA enforcement becomes very difficult when vulnerability data is fragmented across different solutions. Each tool reports issues in its own format, with its own severity ratings and timelines. Security teams are left trying to piece together information from multiple dashboards, which makes it hard to get a clear and consistent view of what needs to be fixed and by when.
Because of this fragmentation, ownership becomes unclear and prioritization often breaks down. Some vulnerabilities may be duplicated across tools, while others are missed entirely. Tracking remediation timelines across teams turns into a manual and error-prone process, making it easy for SLAs to slip. Over time, this leads to delayed fixes, poor accountability, and an increasing level of risk that is not fully visible to the organization.
The SnapSec Perspective: Unified Context Over Siloed Alerts
1. Complete & Always Up-to-Date Asset Catalog
Snapsec Asset Inventory Management (AIM) solves the asset visibility problem by continuously fetching assets from using Cloud Adapters to maintain a live asset inventory. Instead of relying on one-time scans, it automatically includes assets from cloud environments, domains, IP ranges, and other integrated sources.
This ensures that every new asset is tracked as soon as it appears, and removed when it is no longer active. Your asset catalog stays accurate and continuously updated, giving you full confidence in what is being scanned.
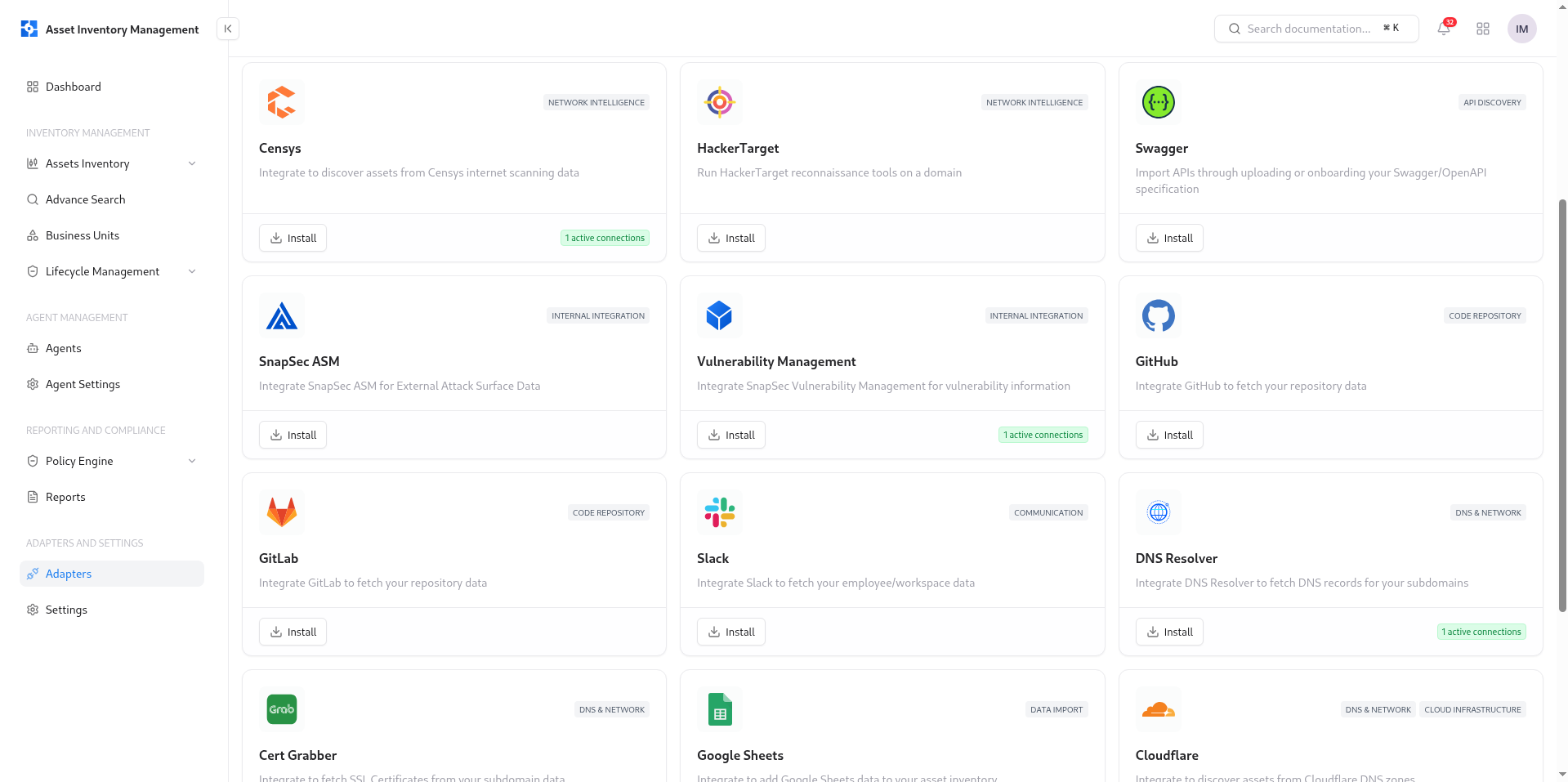
With a complete and real-time inventory, vulnerability scans cover everything that matters, eliminating blind spots and hidden risks.
2. Smart Risk-Based Prioritization
Snapsec Vulnerability Management (VM) introduces a new risk mechanism called True Risk, designed to go beyond traditional CVSS scoring. Instead of relying only on severity, True Risk combines multiple real-world factors such as exposure, asset criticality, business impact, exploit likelihood (EPSS), and known exploited vulnerabilities (KEV).
This gives you a much more accurate view of what actually puts your organization at risk.
As a result, your team no longer wastes time fixing low-impact “Critical” issues while high-risk “Medium” vulnerabilities remain open. Instead, you get a clear, prioritized list of vulnerabilities based on real risk—not just theoretical severity.
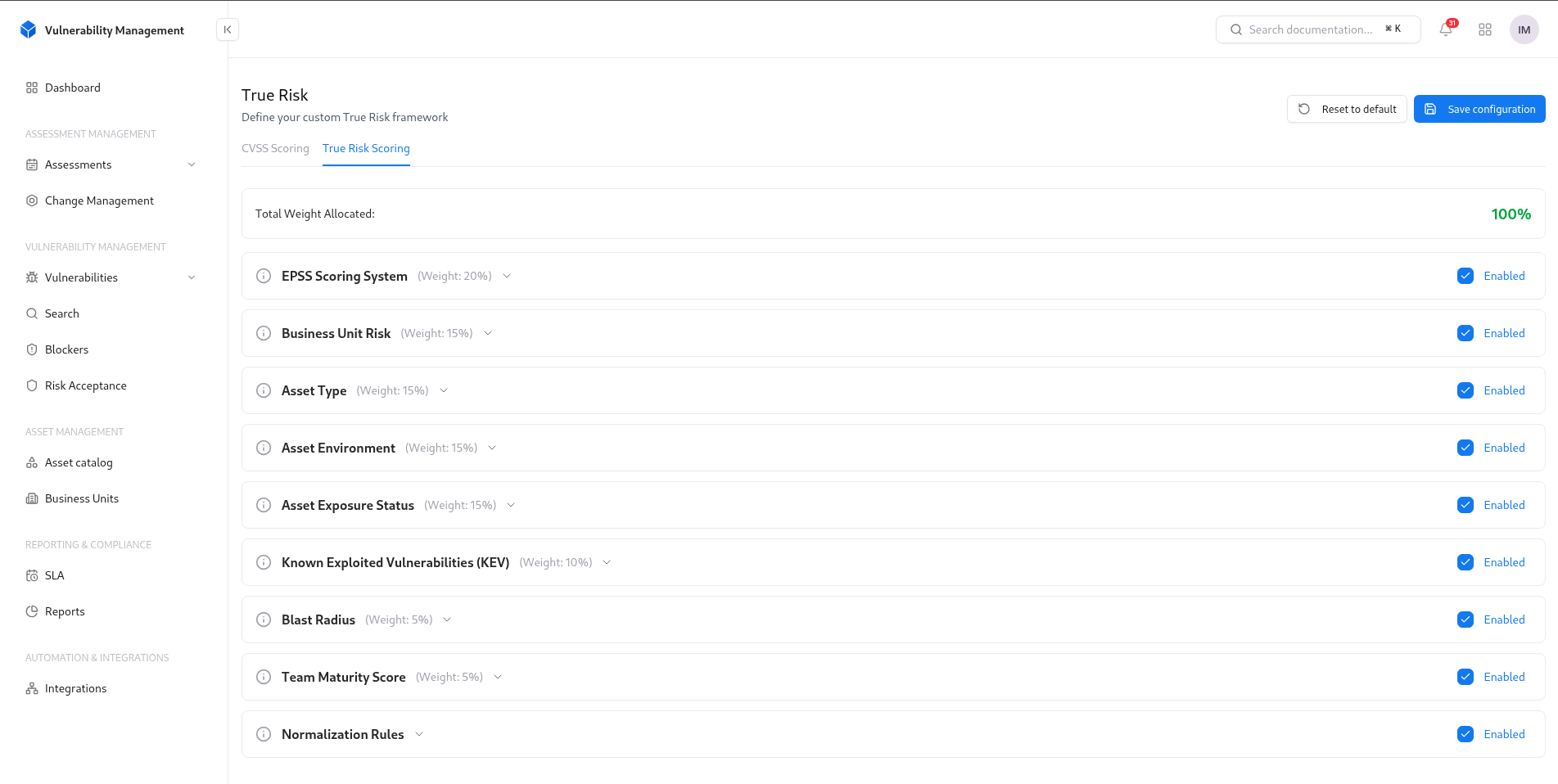
By focusing on True Risk, teams reduce noise, avoid SLA overload, and focus on fixing the vulnerabilities that actually reduce the likelihood of a breach.
3. Centralized Vulnerability View & SLA Tracking
Snapsec Vulnerability Management (VM) aggregates vulnerability data from multiple tools into a single, unified platform. It normalizes findings into one consistent format, removing duplication and confusion.
This allows teams to easily track vulnerabilities, assign ownership, and enforce SLAs without switching between different dashboards.
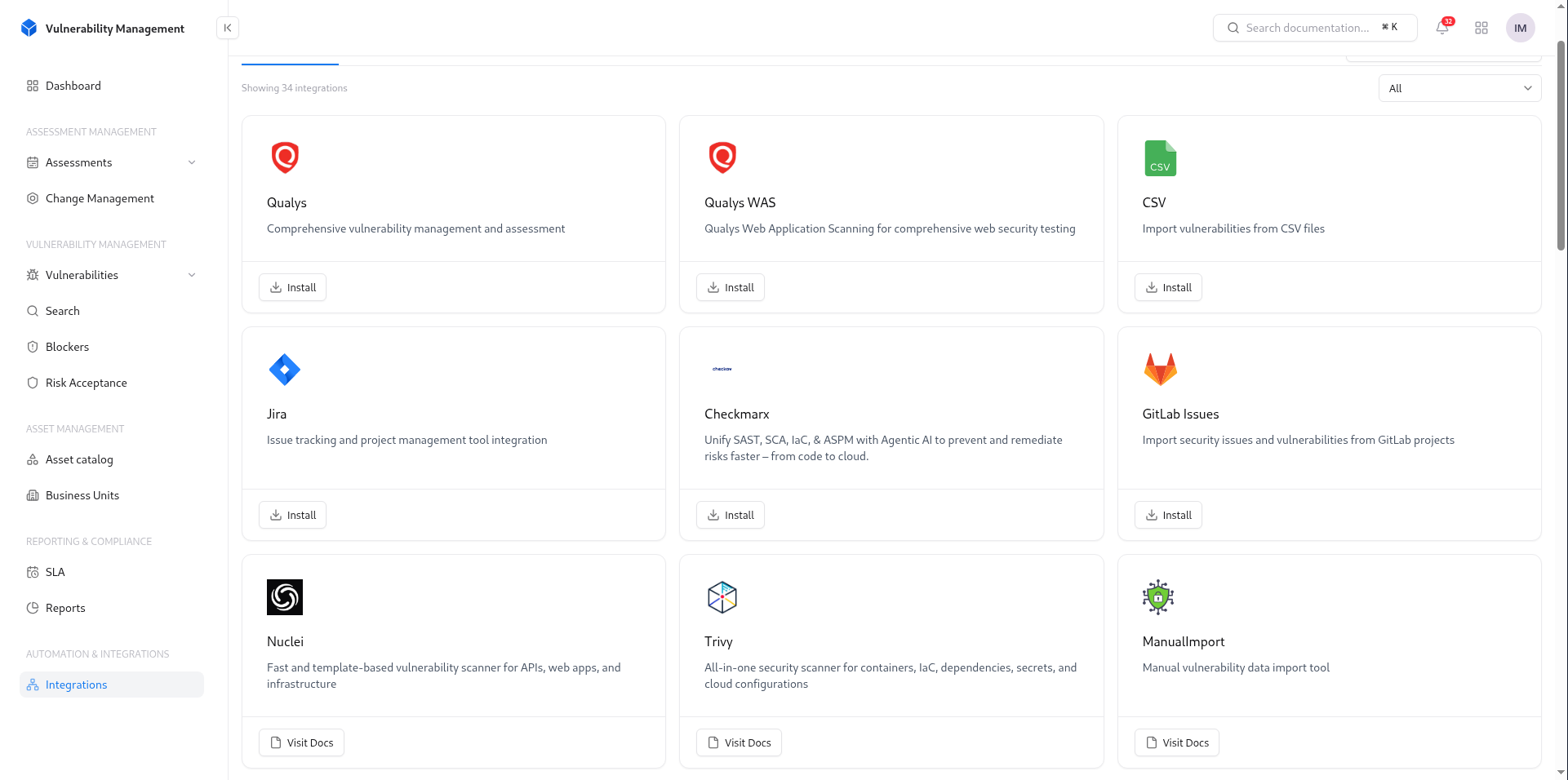
With everything centralized, SLA tracking becomes simple, accountability improves, and no critical issue is missed.
Explore Snapsec Suite Now
Explore Snapsec Suite to see how you can unify asset visibility, prioritize real risk with True Risk, and manage vulnerabilities from a single platform. Get a clear, actionable view of your security posture and start fixing what truly matters—faster and more efficiently.