The Hidden SAMA Gap: Asset Inventory vs Reality
SAMA’s Cyber Security Framework treats asset inventory as a foundational control. Organizations are expected to maintain an accurate inventory of assets, track configuration items, and understand how systems relate to each other. The logic is simple: if you don’t know what you own, you can’t secure it.
But this is exactly where things begin to break.
The assumption behind this control is that asset inventory is already reliable, that organizations have a complete and continuously updated view of their environment. In reality, most inventories are built through periodic updates, stitched together from multiple systems, and rarely reflect the current state of infrastructure. What is documented often lags behind what actually exists.
At the same time, modern environments have become highly dynamic. Assets are created through CI/CD pipelines, deployed across multiple cloud accounts, and exposed through APIs and subdomains that are not always centrally tracked. This introduces a constant stream of assets that fall outside traditional visibility mechanisms.
As a result, asset inventory stops being a source of truth and becomes an approximation. Security controls continue to operate on this incomplete view, creating a gap between what is managed and what is actually exposed. That gap is where risk begins to accumulate unnoticed.
The Assumption That Doesn’t Hold
SAMA’s control assumes that asset inventory is a defined and stable dataset, something that can be maintained, validated, and relied upon across security operations. This assumption made sense in traditional environments where infrastructure changes were controlled and infrequent.
That model no longer applies. Infrastructure today is transient by design. Assets are created and destroyed automatically, services are deployed across distributed environments, and ownership is often decentralized across teams. In such conditions, asset inventory is not something you maintain periodically, it is something that changes continuously.
The gap emerges because most organizations still treat asset inventory as a static function. While the environment evolves in real time, the inventory updates in intervals. This mismatch creates a delay between what exists and what is known, and that delay is enough for exposure to go unnoticed.
Where the Breakdown Begins
In practice, asset inventory is rarely a real-time system. It is typically built from a combination of CMDB entries, cloud exports, and manually maintained records. These sources provide structure, but they introduce latency. By the time assets are recorded, the environment has already changed.
This is where gaps start to appear. A subdomain created for testing never gets added to inventory. An API exposed during development is not documented. A cloud resource deployed in a separate account operates outside centralized visibility. None of these are unusual—they are part of how modern systems are built and shipped.
Over time, these small gaps accumulate. The inventory begins to drift from reality, not because of a single failure, but because the system tracking it cannot keep up with the speed of change. Once that drift happens, every control built on top of the inventory starts operating on incomplete information.
The Visibility Illusion
At this stage, the problem shifts from missing assets to false visibility. From a compliance perspective, everything appears to be working, assets are listed, scans are running, and reports are generated on time.
But all of this operates within a limited, known scope. Anything outside that scope remains invisible, including:
- Unknown subdomains
- Undocumented APIs
- Shadow cloud resources
These assets are often internet-facing and less controlled, making them higher risk. The issue is not that risk is ignored, it is that it is never seen.
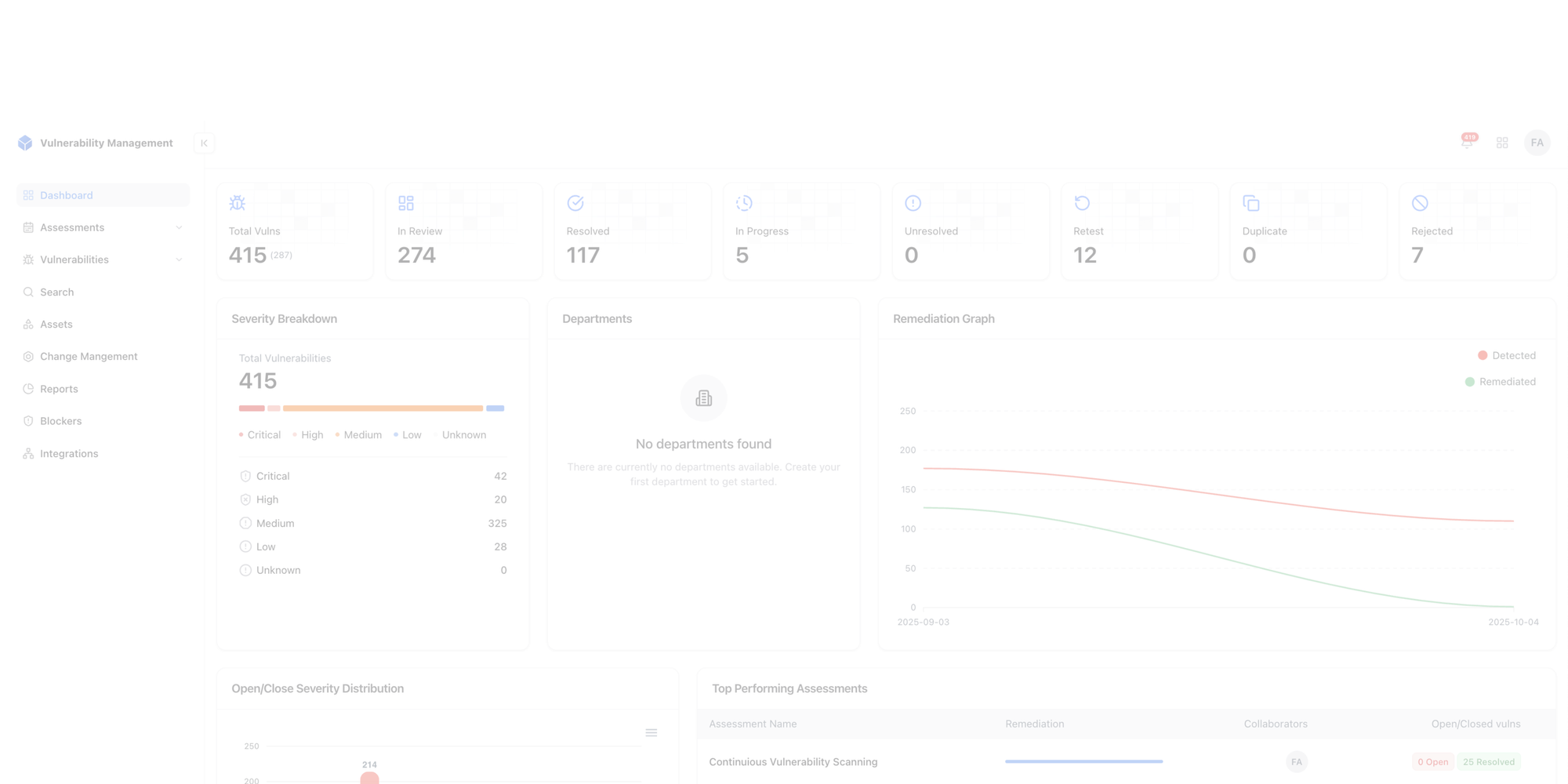
Why This Breaks Vulnerability Management
Vulnerability management depends entirely on asset visibility. It assumes that scanning coverage reflects the actual environment. In practice, teams are scanning everything they know about, not everything that exists.
If an asset is missing from inventory, it is missing from scans, and therefore missing from risk evaluation. This creates a gap where real exposure exists but is never measured.
The result is a misleading sense of control:
- Dashboards look clean
- SLAs are being met
- Reported risk appears low
But none of these reflect the full attack surface. The system is working correctly, just on incomplete data.
The Gap SAMA Doesn’t Explicitly Address
SAMA clearly defines what organizations must do with assets, but it does not address how those assets are continuously discovered. It assumes that asset inventory is already accurate and complete.
In reality, asset discovery is not a one-time activity. It is continuous. New assets are constantly introduced, existing assets change exposure, and some quietly fall out of visibility altogether. Traditional inventory processes are not designed to capture this level of change in real time.
This creates a gap where asset inventory appears structured, but does not fully represent the actual environment. As a result, security controls operate on what is known, while a portion of the attack surface remains outside visibility.
Moving From Static Inventory to Real Visibility
Fixing this is not about improving spreadsheets or refining CMDB workflows. The issue is not tooling quality, but the model itself. A static or periodically updated inventory cannot keep up with an environment that changes continuously.
Asset inventory needs to behave like a live system. Assets should be discovered as they appear, updated as they change, and removed when they no longer exist. Visibility must also extend beyond internal systems to include what is exposed externally, since that is where risk is most immediate.
This shifts the question from “What assets do we have?” to “What assets exist right now?” and that distinction is what closes the gap between assumed visibility and actual exposure.
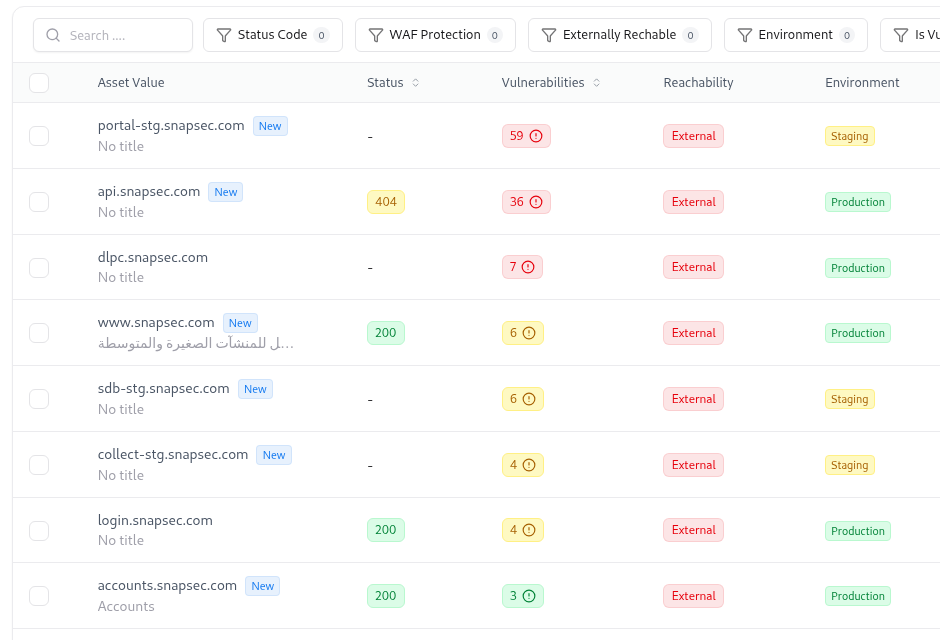
This visibility is not limited to high-level metrics, it extends to actual discovered assets across the environment.
The Snapsec Approach
Snapsec does not treat the asset catalog as a fixed list. Instead, it sees it as something that is always changing. New assets appear, old ones change, and some disappear. So Snapsec keeps the asset inventory “live” by constantly updating it using both Asset Inventory Management (AIM) and Attack Surface Management (ASM).
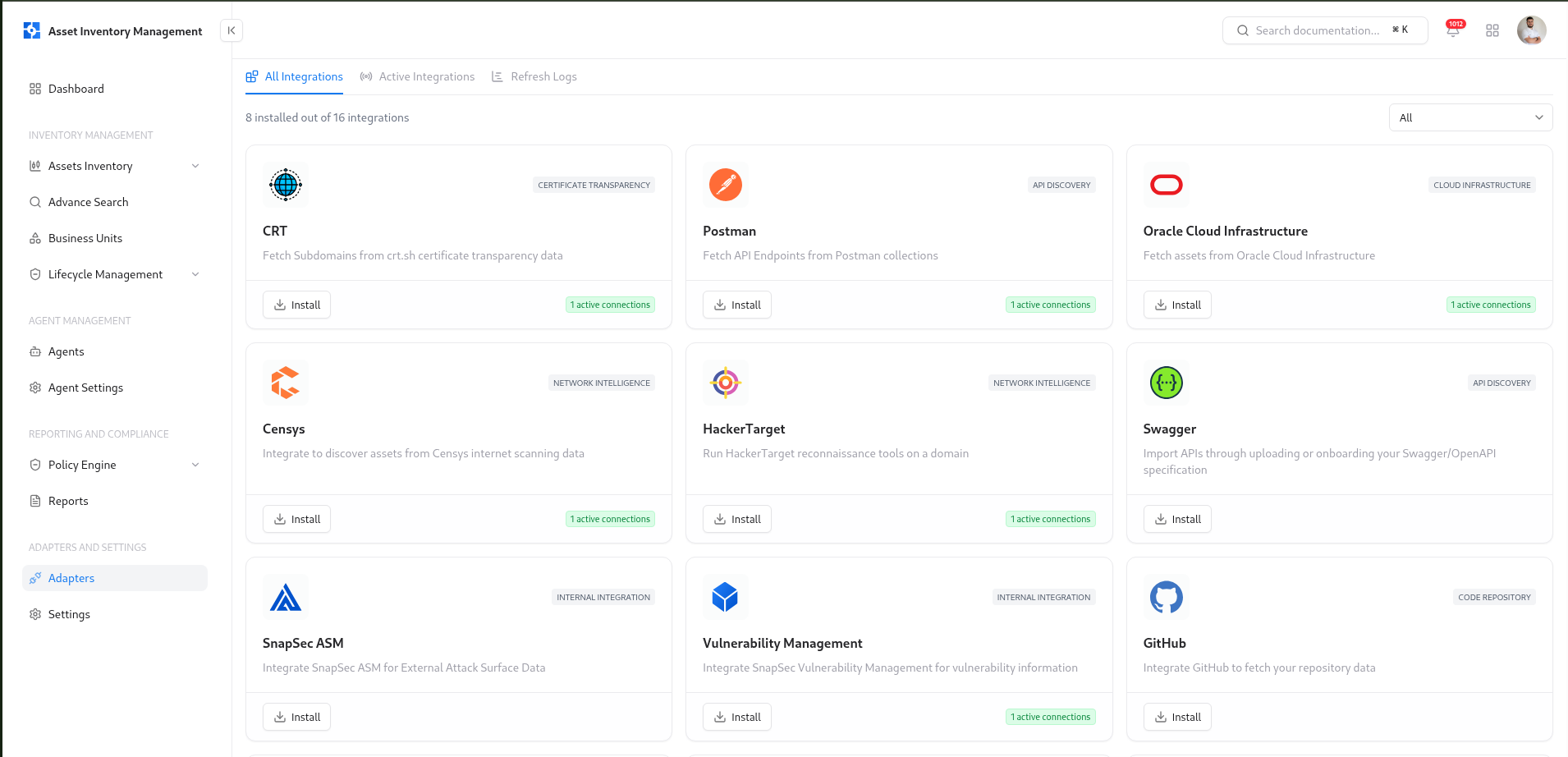
To make this possible, Snapsec uses an adapter-based approach. These adapters connect to different sources like cloud platforms, domains, and external discovery tools. Each adapter brings in data automatically, so assets are added and updated without manual effort. This means the catalog always reflects what actually exists in the environment.
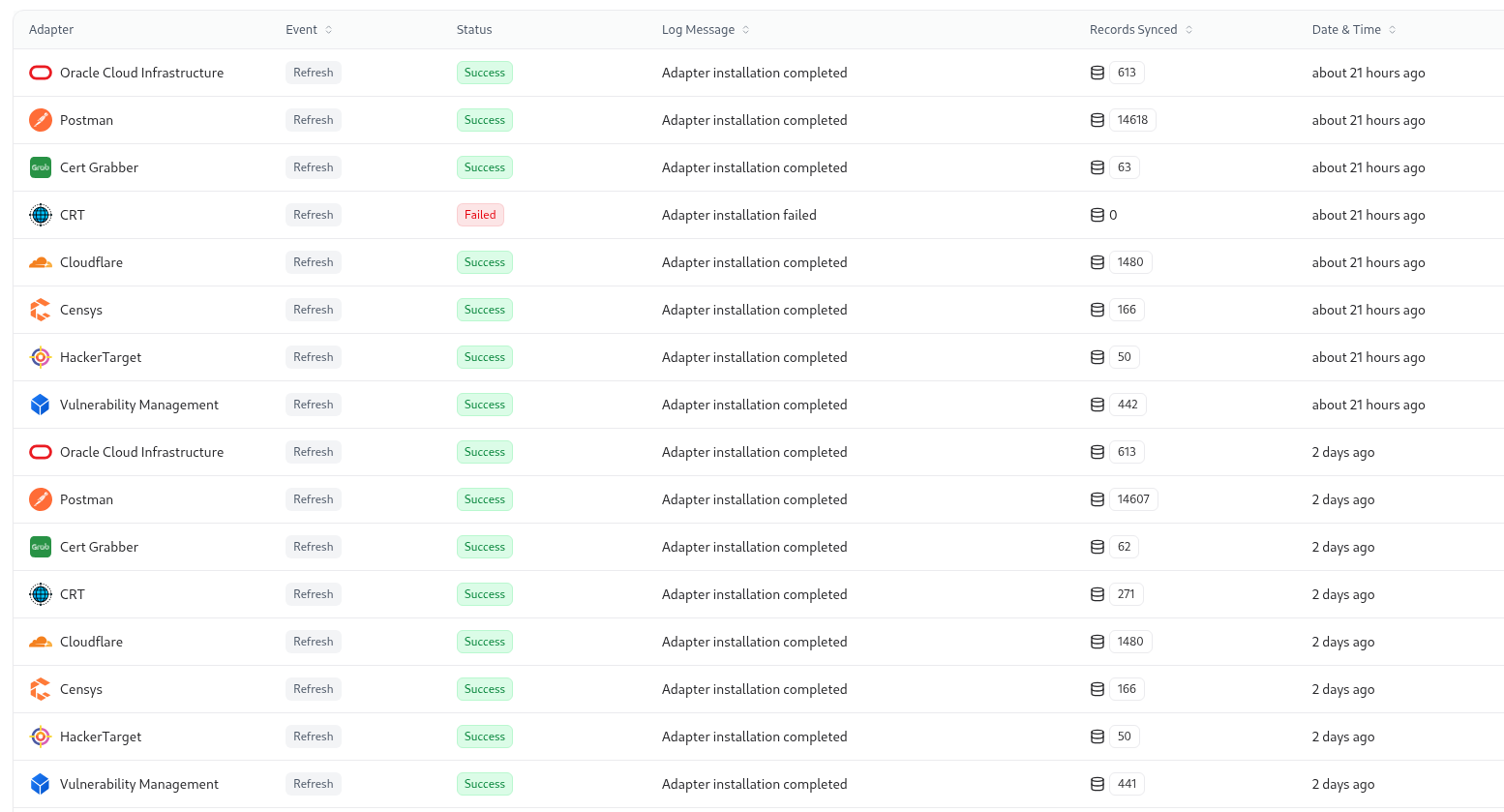
Because of this, security teams don’t have to rely on outdated or predefined asset lists. They get real visibility of all assets, including unknown and internet-facing ones. This helps teams focus on real exposures and manage vulnerabilities based on what is truly present, not what they think is present.
Focusing on What Is Actually Exposed
Not all assets carry equal risk. The most critical subset is the one that is externally reachable. Without clear visibility into internet-facing assets, prioritization becomes inconsistent and often misaligned with actual risk.
Snapsec provides a focused view of the external attack surface, mapping which assets are exposed, how they are exposed, and what services are reachable. This allows teams to shift from broad, coverage-based scanning to targeted remediation based on real exposure, reducing noise and focusing effort where it has the highest impact.
Closing Thought
SAMA’s framework is built on strong security principles, but it assumes something most organizations have not yet achieved: complete and real-time asset awareness. The controls are not flawed, but they depend on a level of visibility that is often missing in practice.
Until asset inventory becomes continuous, dynamic, and externally aware, security operations will continue to function on an incomplete picture of reality. And in security, what remains unseen is usually what gets exploited.
Centralise your Appsec
A single dashboard for visibility, collaboration, and control across your AppSec lifecycle.
Explore Live Demo